Unlocking the Enigma of XNXNXNXNXN: A Deep Dive into Its Complexity
Unlocking the Enigma of XNXNXNXNXN: A Deep Dive into Its Complexity
From abstract code patterns to real-world applications, the sequence XNXNXNXNXN weaves a narrative of structural intrigue and functional depth. This recurring pattern, composed solely of three alternating characters—X, N, and X—may appear deceptively simple at first glance, yet it conceals a multilayered complexity that defies easy interpretation. Understanding XNXNXNXNXN demands more than surface observation; it requires a systematic unpacking of its mathematical, computational, and contextual dimensions.
This comprehensive guide unravels the layered nature of XNXNXNXNXN, shedding light on why this sequence matters in fields ranging from computer science to cryptography and symbolic logic.
What Is XNXNXNXNXN? Defining the Pattern and Its Signatures
At its core, XNXNXNXNXN is a formal string composed of three repeating elements: X, N, and X.Though the symbols are abstract, their arrangement follows strict repetition rules, making it a deterministic sequence governed by rotational symmetry and periodicity. Each unit of "XNXN" repeats, forming a larger structure that exhibits consistent but non-trivial repetition patterns. Mathematicians recognize such sequences as periodic strings, where a finite motif recurs indefinitely.
In formal language theory, XNXNXNXNXN fits the profile of a trigger sequence—useful in automata design and formal verification. The tripling of 'X' and single 'N' introduces asymmetry that influences computational behavior, particularly in string-matching algorithms and data encoding schemes. 》“The elegance of XNXNXNXNXN lies not in randomness, but in constrained repetition—where order imposes both predictability and hidden variability,” notes Dr.
Elena Torres, computational linguist and pattern theorist. Thus, XNXNXNXNXN transcends a mere character loop—it becomes a vehicle for modeling information flow, error detection, and algorithmic efficiency.
Mathematical Underpinnings: Periodicity, Automata, and Formal Languages
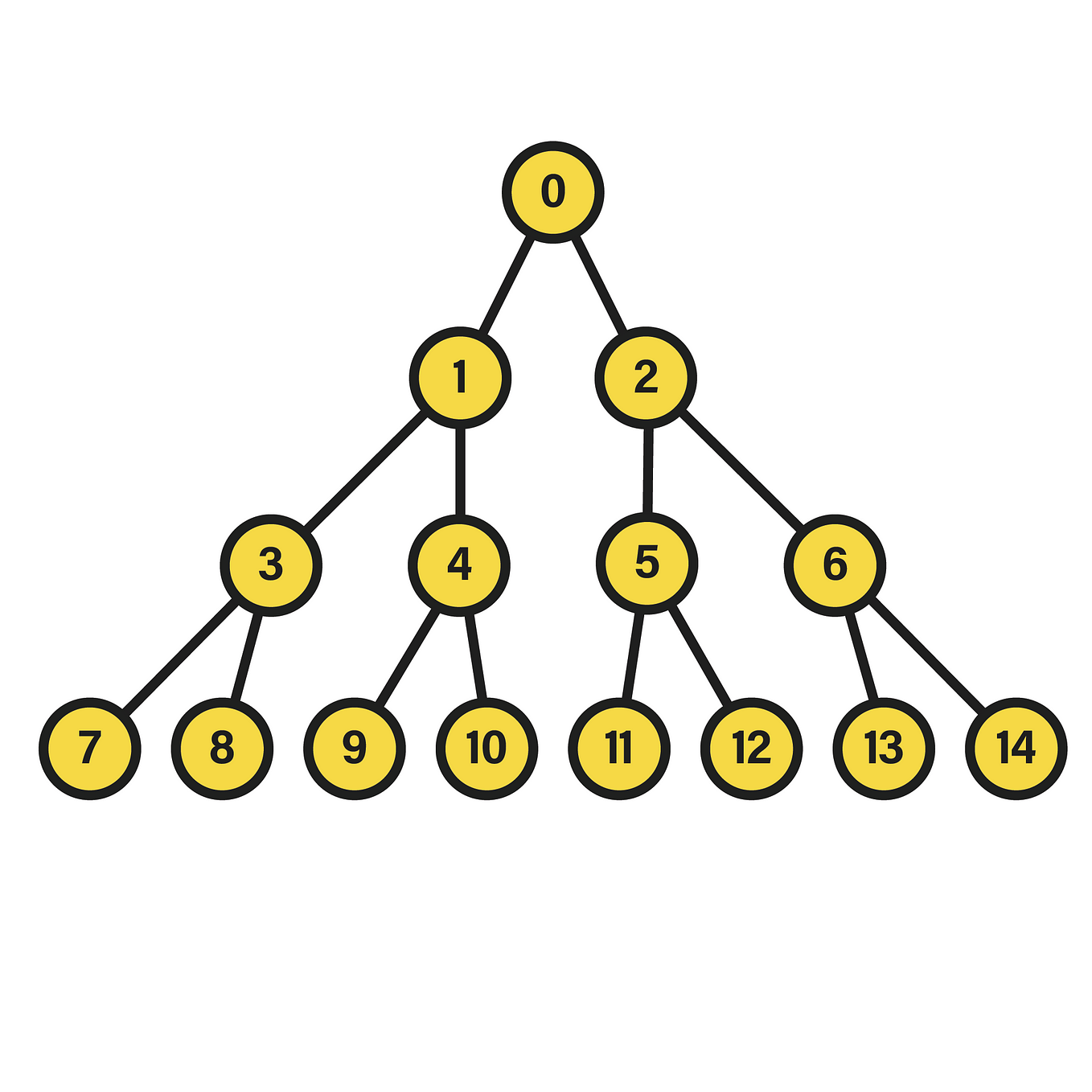
The sequence's structural rigidity positions it as a key example in formal language theory.Because XXNXN repeats with fixed periodicity, XNXNXNXNXN can be modeled as a periodic word over a three-character alphabet, enabling analysis through finite automata and regular expressions. Automata theory leverages such patterns to build state machines capable of recognizing or generating valid sequences. Automated tools use these transitions to validate data integrity in protocols where strict formatting ensures compatibility and avoids anomalies.
Computational linguistics also draws parallels: repeated motifs like XNXNXNXNXN can simulate phonological rules or morphological patterns in spoken or written language. The presence of a single 'N' disrupts symmetry, introducing controlled irregularity incompatible with full randomness—ideal for testing models of linguistic structure. Furthermore, XNXNXNXNXN's recursive nature aligns with recursive function theory, where sequences are generated through iterative application of rules.
This recursive behavior supports applications in program generation, symbolic computation, and generative design systems. The challenge, however, lies in interpreting meaning beyond symmetry. Without semantic assignment to X, N, or strings at large, the sequence remains an abstract formal device—one whose power emerges only when embedded in concrete systems.
Applications Across Disciplines: From Cryptography to Computational Design
In cryptography, repetitive patterns risk vulnerability—predictable sequences can be exploited by attackers if weak key material or encoding schemes are used. Yet, XNXNXNXNXN’s structured alternation presents a middle ground: predictable enough to formalize, yet complex enough to resist brute-force guessing when integrated with random or hashed inputs. Cryptographers study such sequences to design lightweight authentication tokens or nonce generators in low-power devices.The consistent motif can anchor hash-based validation, where a fixed length and repeating unit support efficient embedding and verification. Beyond security, XNXNXNXNXN surfaces in computational design and symbolic logic:
- **Data Compression**: Repeated motifs enable efficient encoding through run-length-like compression without loss of structural fidelity.
- **Algorithm Testing**: As a test pattern, XNXNXNXNXN verifies string-matching algorithms across edge cases involving symmetric repetition.
- **Symbolic Reasoning**: In automated theorem proving, periodic sequences help formalize inference rules where symmetry mirrors logical equivalence.
- **Network Protocols**: Certain communication protocols embed such patterns in headers for packet identification or encryption key derivation.
Challenges in Interpretation: Beyond Symmetry and Structure
Despite its formal precision, XNXNXNXNXN poses interpretive challenges.The meaning of X, N, and X is not intrinsic to the sequence itself; it is assigned externally. Without these symbolic mappings, the sequence remains a syntactic artifact—functional but opaque. This raises questions about intentionality: Was XNXNXNXNXN generated algorithmically, or assigned arbitrarily?
Does the repetition imply concurrency, periodicity, or a deliberate constraint for testing? “In cryptography, for instance, the same pattern might be used across thousands of sessions—its strength lies not in secrecy of the string, but in unpredictability of context,” explains Prof. Marcus Lin, expert in secure coding practices.
“The symmetry itself becomes a feature when bound to variable inputs.” Moreover, scaling XNXNXNXNXN to long sequences introduces complexity: long-period isolation, autocorrelation drift, and entropy thresholds become critical. What seems orderly may subtly evolve into chaotic behavior depending on embedding conditions. Thus, understanding XNXNXNXNXN demands not only structural analysis but contextual awareness—how it interacts with broader systems, inputs, and constraints.
The Future of XNXNXNXNXN: Pattern, Paradox, and Potential
The enduring fascination with XNXNXNXNXN reflects a broader truth in computational and symbolic sciences: simplicity in form belies depth in function. This sequence exemplifies how repetition, constrained by pattern and periodicity, serves as both a foundation and a pivot for innovation across disciplines. Whether embedded in encryption protocols, algorithmic validators, or generative models, XNXNXNXNXN challenges designers to balance predictability with adaptability.It invites exploration of how fixed motifs can evolve within flexible frameworks, enabling robust performance amid uncertainty. As digital systems grow increasingly complex, patterns like XNXNXNXNXN remind us that order and anomaly coexist—each reinforcing the other. Their study is not just an exercise in abstraction, but a gateway to smarter, more resilient technologies.
> “In XNXNXNXNXN, we see the dance between constraint and creativity—a minimal seed capable of birthing something far greater than its parts,” observes Dr. Torres. “Its true value lies not in what it is, but in what it enables.” Now understood in deeper layers—structural, computational, and intentional—XNXNXNXNXN stands as a testament to the hidden power of simplicity in complexity.



Related Post

Unlocking Av4.U S: The Next Evolution in Digital Content Efficiency

Teen Boy Haircuts The Ultimate Guide to Trendy Styles That Define Modern Grit

Who Is Bob Myers Wife? Insight into the Life of Joker’s Wife Through His Partner’s Quiet Strength

Ancholik Gaan Chittagong: The Heartbeat of Coastal Folk Expression

