Unlock Secure, Private, and High-Performance Web Access with PFSense Squid SSL Transparent Proxy
Unlock Secure, Private, and High-Performance Web Access with PFSense Squid SSL Transparent Proxy
At the heart of modern network security lies a seamless fusion of performance, transparency, and encryption—now perfectly embodied in the PfSense Squid SSL Transparent Proxy setup. This powerful combination enables administrators to inspect HTTPS traffic without sacrificing user privacy or network speed, while enforcing granular access controls and centralizing security management. By acting as a transparent gateway that decrypts, inspects, and re-encrypts HTTPS traffic, Squid via PfSense transforms how organizations handle secure web access—without exposing sensitive data or introducing latency.
Understanding how Squid operates as a transparent proxy within a PfSense environment reveals a sophisticated architecture built on trust, efficiency, and security. When end users connect to the network, all HTTPS requests pass through the Squid daemon hosted on PfSense, which sits invisible to clients—preserving seamless browsing. Yet, behind the scenes, Squid performs SSL/TLS interception: decrypting encrypted traffic, scanning for malware, enforcing policies, and re-encrypting data before forwarding it to the destination server.
This process ensures deep visibility across encrypted workloads without requiring certificate installation on client devices or browser updates—critical in today’s encrypted web landscape.
One of the most impactful advantages of using Squid as a transparent HTTPS proxy in PfSense is the ability to maintain full control while mitigating risks. Traditional SSL proxies demand certificate trust administration—users must install intermediary CAs or bypass warnings, disrupting user experience and increasing support overhead.
PfSense automated this complexity: Squid acts as a trusted intermediary, automatically validated by client operating systems, enabling secure monitoring and filtering without user friction. As network security expert Chris Fields notes, “Transparent proxy decryption, when integrated thoughtfully, becomes invisible security—unobtrusive, powerful, and scalable.”
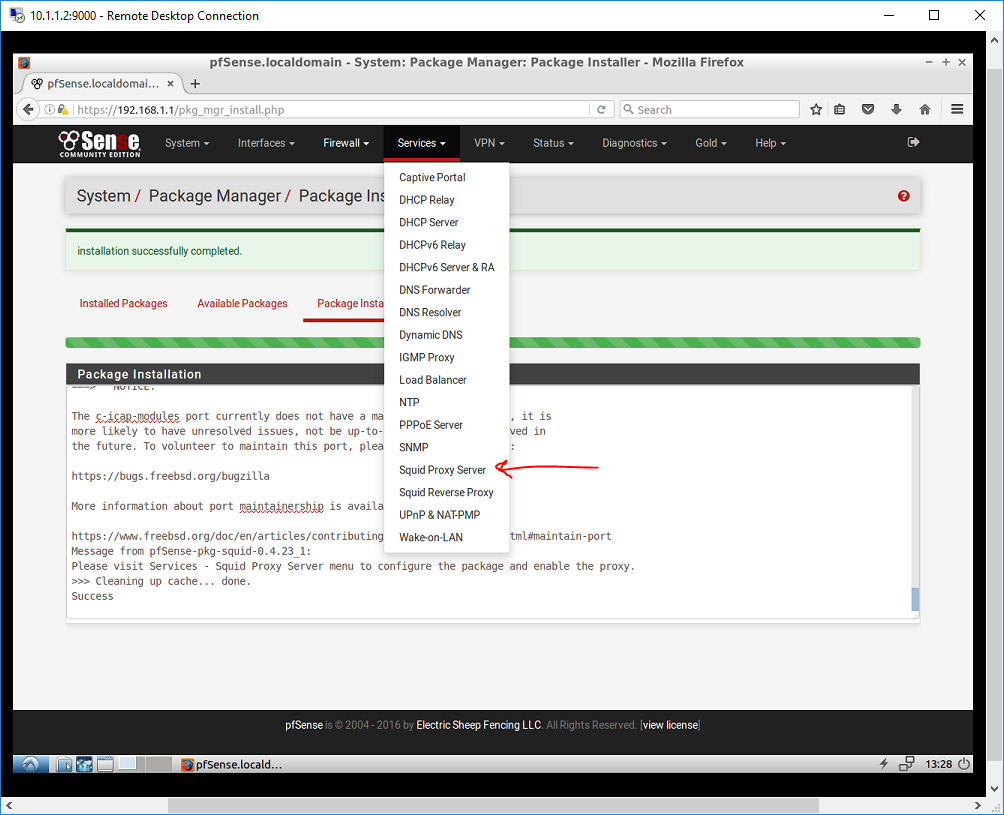
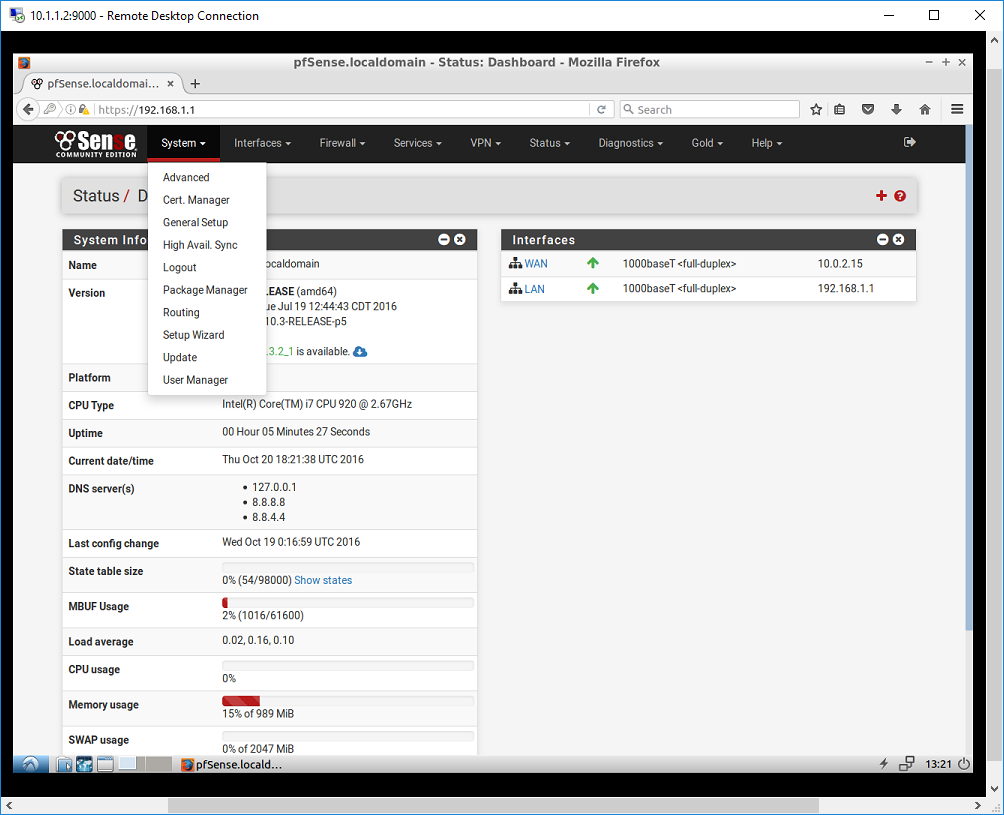
The technical implementation unfolds through careful configuration in PfSense’s web-based interface, primarily via the Squid and SquidManager interfaces. Administration begins by enabling the Squid package and configuring the proxy server’s interface bound to the internal network—often DHCP or a static IP on the VPN or corporate LAN.Critical to the process is enabling SSL interception, which activates certificate authority (CA) issuance within the proxy environment, allowing Squid to generate trusted TLS certificates for decrypted traffic inspection.
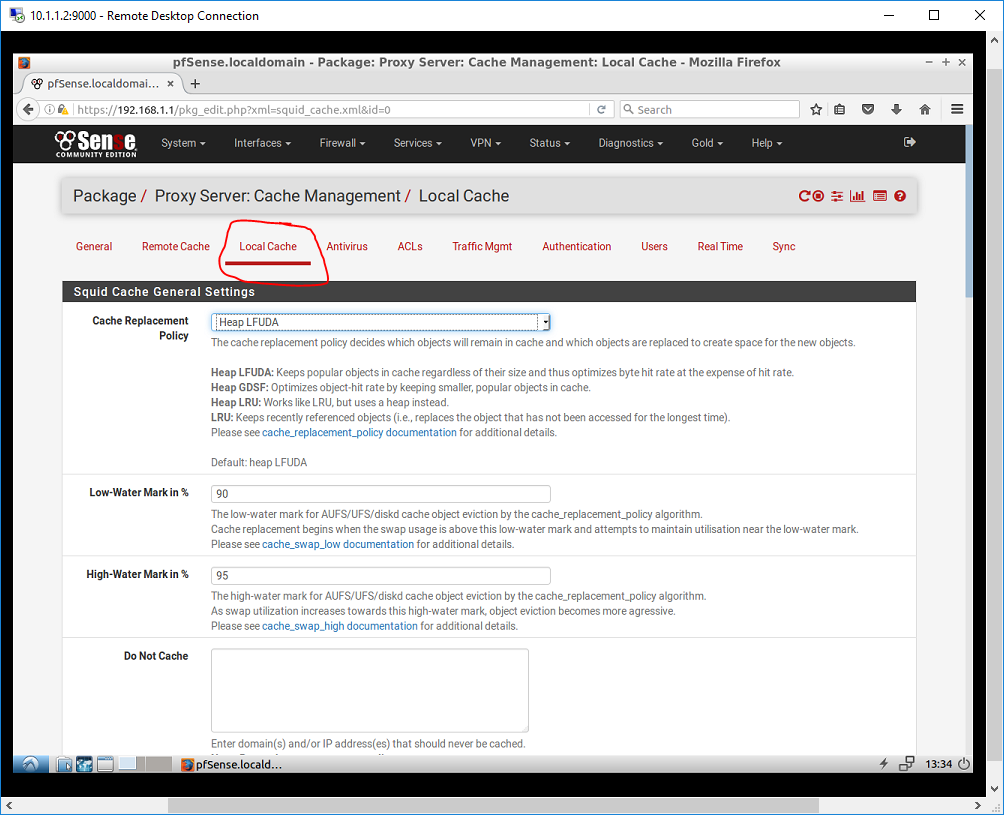
Key configuration steps involve defining source and destination interfaces, specifying audit logging and caching rules, and setting policy directives with granular URL filtering, bandwidth throttling, and session timeouts. For instance, administrators can restrict access to high-risk domains, apply rate limiting to prevent abuse, and cache static content to reduce backend load.
These policies operate transparently—users continue browsing as if routing through a regular gateway, yet every request is evaluated against security rules in real time.
<(H3>Technical Deep Dive: The Encryption Decryption Workflow) The core of Squid’s SSL Transparent Proxy function revolves around a meticulously coordinated decryption-re-encryption cycle. When HTTPS traffic reaches the PfSense proxy, Squid intercepts TLS handshakes using its in-house CA certificate, which clients accept by default—eliminating browser alerts and authentication errors. Decrypted traffic flows through internal rule engines: content filtering engines scan URLs and payloads for malicious signatures, while traffic shaping algorithms enforce bandwidth limits or rate caps.All data is logged in detail for audit purposes before being re-encrypted via the specified surfacing port and relayed to the target web server. This process occurs in milliseconds, preserving performance even under high user loads. <(H3>Operational Benefits and Real-World Impact) Deploying Squid as a transparent proxy within PfSense delivers measurable improvements across operational security and user experience.
Network teams gain centralized visibility into encrypted traffic—critical for detecting data exfiltration, malware propagation, and policy violations without drilling into endpoints. By embedding deep packet inspection within the LAN edge, security posture sharpens without complicating client environments. Moreover, organizations avoid the headaches of manual CA management; Squid automates certificate lifecycle tasks, ensuring consistent trust validation while minimizing administrative overhead.
Practical examples abound: a Midwestern university implemented Squid Transparent Proxy on its PfSense firewall to monitor student and staff HTTPS usage, enforcing acceptable use policies without pushing updates to hundreds of client devices. An EU-based SaaS provider leveraged the same model to inspect encrypted collaboration traffic for GDPR compliance, blocking unauthorized data transfers while maintaining end-user productivity. These deployments underscore a core truth: effective security doesn’t require user disruption—it thrives on seamless integration.
<(H3>Security Considerations and Best Practices) While powerful, the transparency model demands disciplined configuration to prevent security gaps. Certificate trust must be secured—compromising Squid’s CA would undermine the entire proxy trust chain. Best practice mandates restricting the proxy’s administrative access via firewall rules, integrating with RADIUS or LDAP for end-user authentication, and enabling strict logging to detect anomalies.
Additionally, performance tuning—such as cache size and thread limits—ensures the proxy scales with demand without introducing backpressure during peak usage. Network architect Elena Marquez emphasizes, “Transparency creates convenience, but trust must never be assumed. Secure default settings, continuous monitoring, and layered policies—this is how zero-hour vulnerabilities are defended in encrypted environments.”
In an era where 80% of web traffic is encrypted, the ability to inspect HTTPS without undermining security or user experience defines next-generation network management.
PfSense Squid Transparent Proxy transforms encrypted traffic from a black box into a governable asset—offering deep visibility, granular control, and scalable security under a single, invisible gateway. For organizations seeking to future-proof their network infrastructure while empowering IT teams with actionable insights, this combination delivers both strategy and substance.
The PfSense Squid SSL Transparent Proxy is more than a technical tool—it’s a cornerstone of secure, intelligent networking. By enabling real-time decryption, policy enforcement, and centralized oversight without user friction, it sets a new standard for protected, high-performance web access.As digital threats evolve and privacy expectations rise, mastering this proxy model ensures networks stay both resilient and responsive—and that’s the edge every forward-thinking organization needs.

Related Post

From Runway to Resilience: How Karen Elson Redefines Modern Style with Substance and Style

CoolROM PS1: Your Gateway to the Golden Age of PlayStation Gaming

Matthew Perry and Rachel Dunn: A Quiet Partnership That Resonates in Australian Comedy and Beyond

Honoring Life with Grace: The Legacy of High Country Funerals in the High Country

