Token Scammers Exposed: How to Spot and Avoid the Most Dangerous Threats in Crypto
Token Scammers Exposed: How to Spot and Avoid the Most Dangerous Threats in Crypto
In an ever-expanding digital frontier where tokens fuel innovation and speculation, a shadowy undercurrent of scammers has emerged, exploiting the very technology designed to empower. Millions now navigate the volatile world of cryptocurrency, but not all journeys end safely. The rise of sophisticated scam operations—from ‘rogue ICOs’ to deceptive DeFi platforms—has turned crypto from a revolutionary force into a high-stakes gamble fraught with hidden dangers.
This article cuts through the noise to reveal the most prevalent scams, red flags every user should know, and essential strategies to protect assets in a landscape rife with deception.
While blockchain technology promises transparency and decentralization, its anonymity and global reach also attract malicious actors who manipulate both codes and people. As reported by cybersecurity firms and financial watchdogs, over 80% of crypto investors have encountered a scam at some point, with losses exceeding $1.7 billion in 2023 alone.
These numbers underscore the urgent need for awareness. Unlike traditional financial systems, crypto transactions are often irreversible—meaning caution is not optional, it’s imperative.
Spotting the Scammers: Common Crypto Scams Everyone Should Recognize
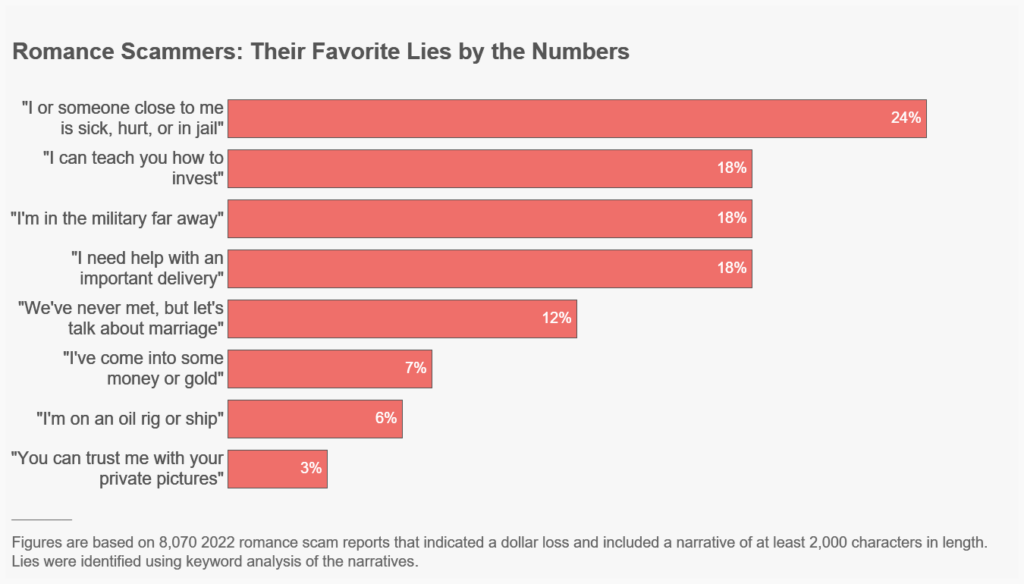
Understanding the tactics used by scammers is the first line of defense. Below are the most prevalent types of token scams infiltrating the crypto space.Fake ICOs and Token Schemes
Initial Coin Offerings (ICOs) were once praised as democratized fundraising tools, but many have devolved into scam vehicles. Scammers launch elaborate but fraudulent tokens—often using glossy whitepapers, celebrity endorsements, and fake communities—only to disappear with investor funds. “These ICOs mimic legitimate launches but lack real utility or development,” explains Dr.Elena Torres, a blockchain forensic analyst. “They promise outsized returns with no clear roadmap, then vanishes—often encrypted offshore.” Investors should verify project teams through public blockchain records, audits (publicly verifiable), and prior track records. Legitimate ICOs are transparent, with legal entity details and technical whitepapers available on independent platforms like Etherscan.
Phishing and Social Engineering Attacks
Phishing remains one of the most pervasive threats. Scammers deploy deceptive emails, fake websites, and SMS messages designed to mimic trusted exchanges or protocols. These convincing ruses trick users into sharing private keys, seed phrases, or two-factor codes.“A well-crafted phishing campaign can parasite into your device via a burner email that looks identical to Binance’s,” warns cybersecurity expert Marcus Reed. “Once gained, attackers hijack wallets and drain funds in minutes.” Users must enable multi-factor authentication (MFA) where available, verify URLs manually (look for HTTPS and misspellings), and never expose seed phrases or passwords under any online communication.
Faux Wallet and Exchange Apps
Scammers distribute counterfeit apps—available via third-party app stores or fake links—that replicate the look of popular wallets like MetaMask or Trust Wallet.These malicious clones intercept private keys during transactions, encrypting access or stealing funds outright. “The apps often look identical, even down to the logo and interface, but run on stolen servers,” says cybersecurity firm Kaspersky. “Always download wallets directly from official sources, and cross-check app signatures using trusted blockchain explorers.”
Affiliate and Referral Fraud Schemes
Scammers recruit investors through built-in referral programs, offering steep rewards for bringing in new users.These networks operate like pyramid structures—prioritizing recruitment over project viability. “This model incentivizes fake sign-ups and misleading promotions,” notes crypto compliance expert Fatima Ndiaye. “Angry users often realize too late the scheme collapses when payouts stop or demand drops.” Due diligence includes investigating referral moderation policies, checking active user bases, and validating project fundamentals beyond promotional hype.
To build personal defenses, investors should adopt a disciplined approach: verify legitimacy before engaging, treat private keys as unrecoverable, and treat unsolicited “hot tips” or overnight returns with deep skepticism. Community resources, such as reputable Crypto Scam Patrol databases and transaction trackers, provide real-time alerts and verified project histories. Platforms like Certificate biases.Coin and Blockchain Transparency Initiative publish forensic reports that expose suspicious contracts and projects before they damage new investors.
Essential Safety Practices for Token Holders
Protecting crypto assets requires more than just technical tools—it demands behavioral discipline.Top recommendations include: - **Cold Storage Usage:** Keep the majority of funds offline in hardware wallets; only store minimal reserves on active devices. - **Source Verification:** Confirm URLs, app signatures, and project team identities through official channels—not third-party clicks. - **Transaction Review:** Always double-check wallet addresses and contract hashes before confirming transfers—even for known contacts.
- **Regular Audits:** Use blockchain explorers to inspect token contracts for unusual spending patterns or hidden kill switches. - **Education:** Stay updated on emerging fraud tactics—many scams mimic new DeFi innovations or NFT-based hype.
The cryptocurrency landscape is not inherently dangerous—but neither is it immune to intelligent, adaptive scammers.By marrying technical safeguards with sharp awareness, users reclaim control over their digital wealth. The key lies in skepticism, due diligence, and a network of trusted intelligence. In a world where trust is fragile and innovation fast, staying one step ahead means knowing who to trust—and who to watch.
The path forward is clear: vigilance transforms vulnerability into resilience, empowering safe participation in the crypto future.



Related Post

The Magical World of Sonny Bono Kids: Where Nostalgia Meets Imagination

Agnes Moorehead Nude: Unveiling the Icon’s Bold Choice and Cultural Resonance

Tim Matheson’s Wife: Behind the Iconic Star’s Public Persona and Private Life

Dojo Masters WSJ Crossword Clue Puts Focus on the Enigmatic Architect of Puzzle Royalty