Samsung Knox: The Security Platform That Powers Enterprise Trust
Samsung Knox: The Security Platform That Powers Enterprise Trust
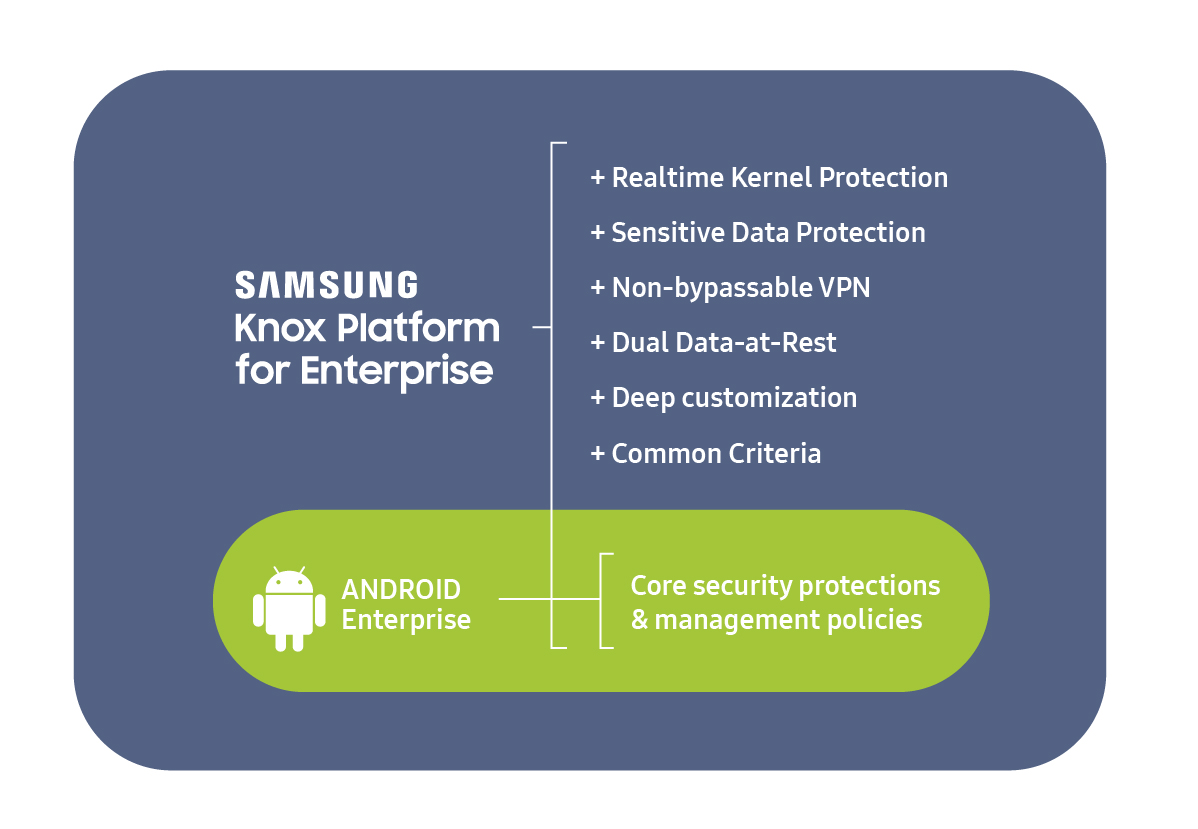
In an era where digital threats evolve faster than defenses, Samsung Knox stands out as a gold standard in enterprise mobility and device security. More than just a suite of tools, Knox is a holistic security platform designed to protect smartphones, tablets, laptops, and embedded systems across enterprise environments. It combines hardware-rooted security, advanced encryption, secure boot processes, and deep integration with operating systems—all engineered to deliver uncompromised protection without sacrificing user experience.
As organizations increasingly rely on mobile devices for mission-critical operations, understanding how Samsung Knox works is essential for anyone navigating the landscape of secure technology.
Built on Samsung’s decade-long investment in secure hardware and software integration, Knox operates at every layer of the device stack—from the root of trust in silicon to the user interface. Unlike generic security software, it leverages dedicated secure elements (SE) and trusted execution environments (TEE) embedded directly into device chips.
“Knox is designed so that security is not an add-on but built in at the firmware level,” explains a Samsung security architect. This architectural approach ensures even sophisticated attacks—like firmware-level malware or side-channel exploits—face near-impossible barriers.
Core Pillars of Samsung Knox: Hardware, Software, and Trust
At its foundation, Knox integrates three critical components: secure hardware, trusted software, and cryptographic guarantees.Security begins with hardware rigor. Samsung embeds secure elements—unhackable chips responsible for storing cryptographic keys and authenticating device integrity. These elements are isolated from the main processor, ensuring even root-level compromises cannot breach protection.
When a user powers on a Knox-enabled device, safe boot protocols verify every system component, rejecting unauthorized code before launch. “Our secure boot chain traces back to the silicon itself,” the architect notes, “making tampering detectable at the earliest stages.” Paired with this hardware foundation is Knox’s trusted operating layer. Knox enhances both Samsung’s Knox OS on mobile devices and Samsung Knox for Android and Windows devices, providing hardened environments where sensitive data and enterprise apps run in isolated containers.
This trusted execution environment shields confidential operations—from financial transactions to government communications—from malicious or compromised apps. Users benefit from cryptographic attestation: daily verification that the device remains trustworthy, reinforcing confidence in its integrity. Kernel-level integration further strengthens Knox’s defenses.
By patching vulnerabilities before they surface and limiting permissions at the OS core, Samsung ensures every interaction is scrutinized. This proactive posture means Knox platforms detect and neutralize threats in real time—before they compromise user data or corporate networks.
Real-World Applications: Securing Enterprise Workforces
Organizations across healthcare, finance, defense, and telecommunications have adopted Samsung Knox to safeguard mobile employees and protect sensitive infrastructure.For example, healthcare providers use Knox to secure patient data accessible via mobile devices, ensuring HIPAA compliance through end-to-end encryption and strict access controls. In banking, Knox prevents unauthorized access to transaction systems, even if devices fall into the wrong hands—thanks to encrypted clipping and biometric authentication layered within the platform. Public sector agencies rely on Knox to deploy secure field operations tools, where confidence in device integrity directly impacts mission success.
Military and government users benefit from tamper-resistant chipsets that protect classified communications and operational data against advanced cyber threats. Observe that Knox’s adaptability extends beyond consumer devices: Knox for Samsung Devices and Knox Asia’s customized enterprise editions illustrate Samsung’s commitment to flexible, scalable security tailored to diverse organizational needs.
Equally powerful is Knox’s enterprise management suite.
Admins gain centralized control over device policies, remote wipe capabilities, app blacklisting, and compliance monitoring—all enforced through a secure management console. This gives IT teams not only oversight but also assurance that every endpoint adheres to strict security baselines, reducing the attack surface comprehensively.
End-to-End Encryption and Zero-Trust Principles
Encryption lies at the heart of Knox’s protection model.Data stored on devices—including messaging, files, and credentials—is encrypted using AES-256, the cryptographic gold standard. Knox ensures keys remain locked within secure elements, accessible only through biometric or PIN-based authentication. Even if physical access occurs, the secure enclave shields keys from extraction or cloning.
Complementing this is a strict zero-trust architecture: trust is never assumed, always verified. Every app, network connection, and data transfer is authenticated and authorized in real time. This means a stolen device cannot silently exfiltrate data, as Knox denies unauthorized runtime access and triggers automatic lockdowns when anomalies occur.
“We design Knox so that security evolves with each threat,” a technical lead asserts. “Every patch, every update strengthens the trust layer.”
The Future of Secure Mobility with Samsung Knox As mobile devices grow deeper into every aspect of professional and personal life, the demand for breakthrough security platforms intensifies. Samsung Knox answers this call with a unified, hardware-backed strategy that transforms devices into trusted extensions of enterprise networks.
Its blend of tamper-proof hardware, secure software layers, and enterprise-grade management positions Knox not just as a product, but as a critical pillar of modern digital trust. In essence, Samsung Knox proves that true security isn’t an afterthought—it’s engineered from the ground up. For organizations demanding unwavering protection across an expanding digital frontier, Knox sets the benchmark.
It doesn’t just secure devices; it safeguards operations, privacy, and confidence property the most critical assets in today’s connected world.
As cyber threats escalate and digital dependency accelerates, Samsung Knox stands as a benchmark in enterprise security—proving that true protection is built on a foundation of trust, data, and resilience. In a landscape where breaches threaten livelihoods, Knox isn’t just a feature: it’s a necessity.



Related Post

Unveiling The Life Of Mark Ruffalo's Wife A Deep Dive Into Their Journey Together

Oliver Jackson-Cohen Partner Reveals The Unseen Forces Reshaping Modern Business Strategy

The Enchanting World of Berry Creams: Where Fairy Magic Meets Flavor Fusion

NYPD Blues: Dennis Franz’s Fury When the Real Streets Broke Silence

