Prolaco Malware: Unpacking Its Devastating Tactics and the Hidden War in Cyber Defense
Beneath the surface of cyberspace, a stealthy digital predator operates in the shadows—Prolaco Malware, a sophisticated threat weaponized by advanced cyber actors to dismantle corporations, corrupt data, and dominate the hidden war of digital defense. Unlike flashy ransomware campaigns, Prolaco’s tactics are insidious, blending stealth, persistence, and precision to compromise systems undetected for months, extracting critical intelligence before disappearing like smoke. As organizations grapple with escalating cyber threats, unpacking Prolaco’s operational blueprint reveals not just the mechanics of its attack, but the evolving arms race between defenders and adversaries in an era where data is currency and war unfolds in bytes.
Decoding Prolaco Malware: Structure, Purpose, and Digital Espionage
Prolaco Malware represents a new class of advanced persistent threat (APT) tools, engineered not for immediate destruction but long-term surveillance and information harvesting.Its modular architecture enables adversaries to customize payloads based on target profiles, making it a highly adaptive instrument of cyber espionage. At its core, Prolaco infiltrates networks through stealthy initial access vectors—often phishing lures or zero-day exploits—then establishes a foothold by disabling security tools and moving laterally across systems. Unlike commodity malware, it leaves minimal traces, using encrypted communication channels and rootkit-like techniques to remain undetected for extended durations.
“This isn’t ransomware—it’s reconnaissance,” explains cybersecurity researcher Dr. Elena Markov, who has studied Prolaco’s behavior in real-world breaches. “The malware’s strength lies in its patience: it waits, observes, and collects—then exfiltrates only when the time is perfect.” Prolaco’s operational design reflects a shift from overt cyberattacks to covert influence campaigns.
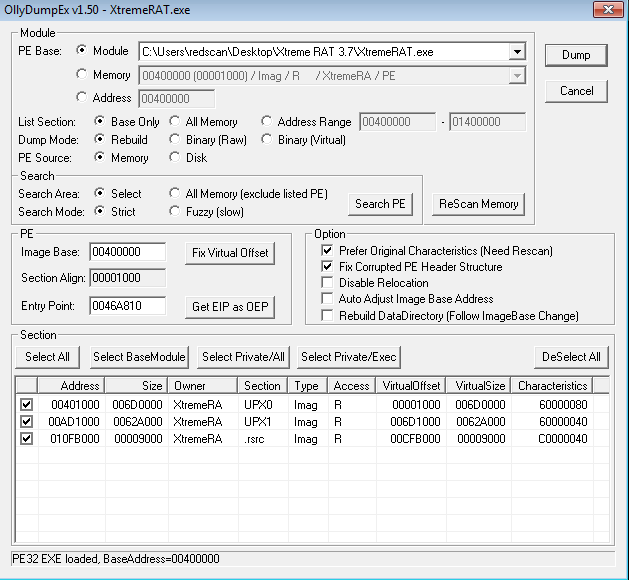
Its payloads include keyloggers, credential stealers, and remote access trojans (RATs), each crafted to serve distinct intelligence-gathering goals, from stealing intellectual property to monitoring executive communications. Once deployed, it mellows into the network, replicating silently, disabling endpoint protection, and launching periodic data extraction cycles that evade standard detection systems.
Infiltration Methods: How Prolaco Slips Into Corporate Networks
Prolaco’s entry into secure environments relies on calculated deception and technical precision.The most common triggers are targeted phishing emails masquerading as trusted internal communications, often laced with malicious macros or embedded in spoofed domain URLs. Once a user engages with these lures, Prolaco rapidly deploys dependent components—downloader executables or boilerplate scripts—ensuring initial compromise even against basic sanitization tools. Beyond phishing, Prolaco exploits zero-day vulnerabilities in software and firmware, allowing it to bypass patched defenses.
Once inside, attackers use logical exploitation—leveraging misconfigurations or idle admin accounts—to navigate laterally with surgical precision. “The malware thrives on patience,” notes threat intelligence analyst Marcus Reed. “It doesn’t rush; it maps the network, identifies high-value assets, and moves only when the risk is calculated low.” Adding to its stealth, Prolaco leverages living-off-the-land binaries—legitimate tools repurposed for malicious ends—making detection significantly harder.
By injecting code into trusted processes like PowerShell or Windows Management Instrumentation, it camouflages its activities within normal system behavior, bypassing conventional signature-based defenses.
Persistence and Resilience: The Art of Unseen Command
Once installed, Prolaco establishes durable persistence mechanisms designed to outlast security updates and temporary countermeasures. Attackers employ techniques such as scheduled task creation, registry persistence, and service injections that reactivate the malware even after system reboots or reboots initiated by update workflows.Prolaco’s payloads often autocensor at inbound connections to avoid triggering anomaly-based detection, communicating only through obfuscated channels that mimic legitimate traffic patterns. Equally critical is its anti-deletion logic: rather than erasing itself, Prolaco deletes its own traces or triggers scheduled self-sterilization routines—all while preserving core components. This balance ensures operational continuity even under aggressive forensic scrutiny.
“This resilience isn’t accidental,” says Reed. “Prolaco’s design reflects years of refinement by developers who understand how threat defenses work—and how to outsmart them.” Moreover, Prolaco demonstrates behavioral mimicry: mimicking user activity, normal data flows, and background processes to avoid raising alerts. This level of sophistication blurs the line between legitimate system operations and intrusive malware, challenging even seasoned defenders to separate noise from genuine compromise.
Countering the Shadow War: Defense Challenges and Strategic Emergence
Defending against Prolaco demands a paradigm shift from reactive patching to proactive, behavior-centric defense strategies. Traditional signature-based antivirus tools prove inadequate against its polymorphic and zero-day exploits, exposing critical gaps in enterprise cybersecurity postures. As Prolaco evolves through machine-assisted adaptation, defenders face an uphill battle: detecting threats that blend in, moving silently, and striking precisely when defenses are weakest.Organizations must adopt layered security models integrating advanced EDR (Endpoint Detection and Response) platforms, behavioral analytics, and continuous network monitoring. Crucially, user training remains a frontline defense—phishing simulations and awareness programs disrupt initial access vectors hands-on. “Prolaco thrives on human oversight and delayed detection,” explains Markov.
“The real vulnerability isn’t just technical; it’s organizational.” Incident response plans must also evolve: rapid containment, forensic depth, and real-time threat intelligence sharing are essential. As Prolaco’s tactics mature, so too must countersafe measures—turning the tide in the invisible war that defines modern cyber defense. In the ongoing battle between disruption and protection, Prolaco Malware stands as both warning and catalyst—a stark reminder that the digital frontier is no longer a battlefield of firewalls and VPNs alone, but a clandestine war of precision, patience, and persistent threat.


Related Post
Prolaco Malware: The Silent Invasion Reshaping Cyber Defense’s Battleground
Chicago’s Top D1 Teams: Where the Slam Dunk Defines Dominance
Tia Mowry & The Power of Authentic Celebrity Voice: Reshaping Hollywood’s Tapestry

The Search That Won’t Fade: Unraveling the Mystery of Rebecca Lowe’s Missing Person Case

