Install PfSense on FortiGate: Master Hybrid Network Security with a Single Step
Install PfSense on FortiGate: Master Hybrid Network Security with a Single Step
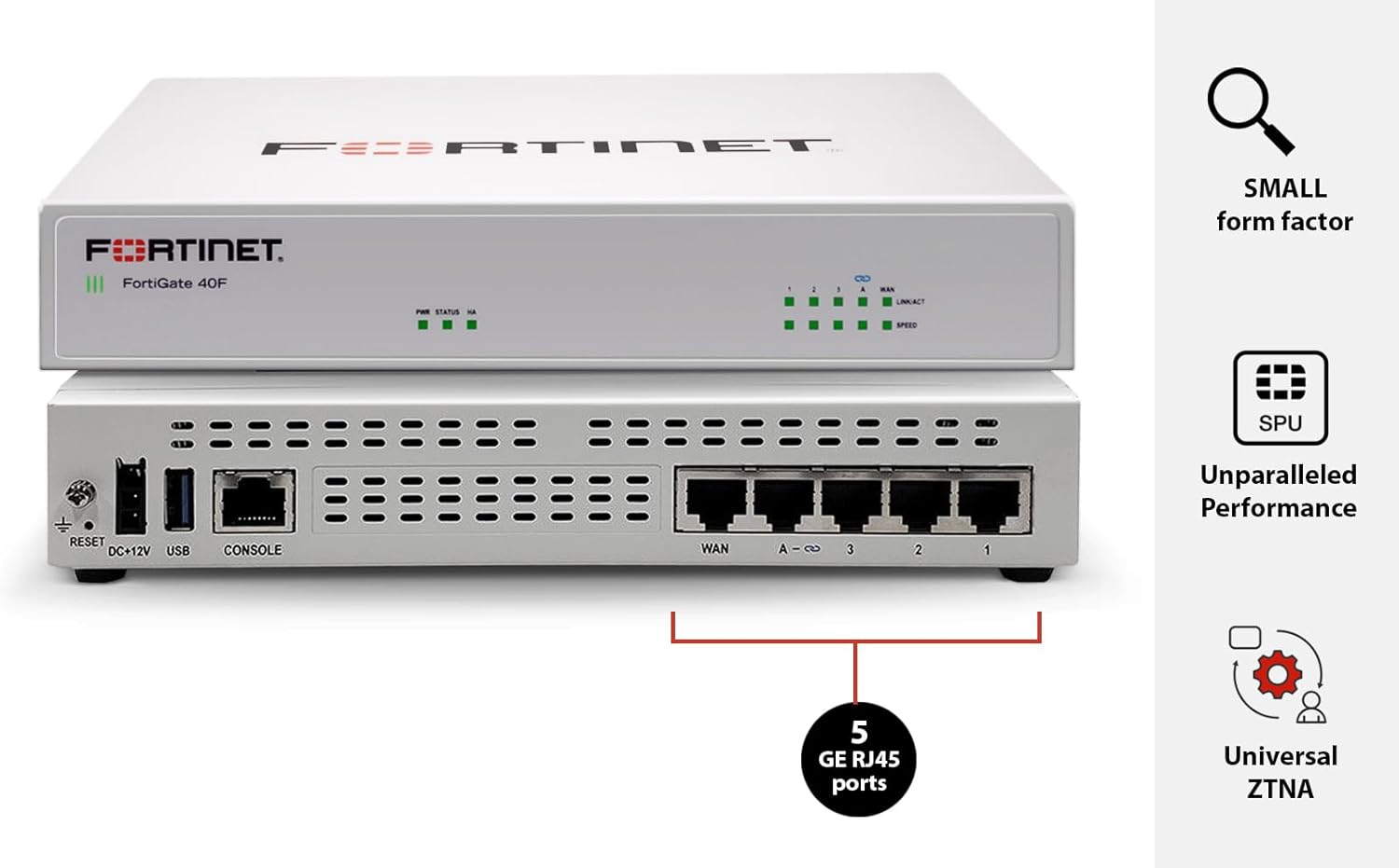
For network administrators seeking a powerful, open-source firewall solution with enterprise-grade functionality, deploying PfSense on FortiGate transforms network infrastructure—combining the robust security of FortiGate hardware with the flexibility of PfSense’s intuitive OS. This integration unlocks advanced firewalling, VPN support, traffic analytics, and seamless failover, all within a single, scalable platform. By merging FortiGate’s optimized throughput with PfSense’s extensive firewall rules and application control, users gain a next-generation firewalld layer for modern, hybrid environments.
Instruction operators, tone down the technical hurdles: installing PfSense on FortiGate is not only feasible but delivers tangible advantages in security, performance, and operational simplicity. The process leverages FortiGate’s hardware foundation while injecting PfSense’s open-source intelligence and deep customization. This guide delivers a precise, step-by-step roadmap—designed for practical implementation by both seasoned engineers and those new to hybrid firewalls.
Why Combine FortiGate and PfSense?
Understanding the Architecture Advantage FortiGate’s hardware delivers high performance and built-in security features, while PfSense—built on FreeBSD—offers unparalleled flexibility with its open-source firewall engine, customizable dashboard, and rich plugin ecosystem. Together, they create a hybrid model that balances raw speed with administrative control. The integration supports: - Layer 3–7 packet inspection with stateful firewalling - IPS and VPN tunneling securely over encrypted channels - Traffic shaping and QoS rules to prioritize critical applications - Centralized logging and monitoring via PfSense’s intuitive interface - Failmap failover for zero downtime during hardware or network outages As network architectures evolve toward cloud-connected, mobile-first environments, the demand for a unified, scalable security layer grows.
This combination delivers precisely that—offering a bridge between legacy FortiGate deployments and the future of open firewall platforms.
Pre-Installation Requirements: Laying the Groundwork
Before beginning the installation, ensure your FortiGate model supports GrooveOS (FortiOS), as PfSense runs on the Groove-based containerized environment. Verify hardware compatibility: minimum 4 GB RAM (8 GB recommended), at least a dual-core CPU, and sufficient storage (30 GB available space, larger for multi-network setups).Equally critical are preparation steps: backup existing FortiGate configurations and network rules—this step prevents loss during migration. Disconnect from the network temporarily during setup to avoid configuration conflicts. Download the official PfSense ISO from
Step-by-Step Installation: Installation 101 with Real-World Precision
Begin by updating the FortiGate’s system image. Log in via FortiOS web GUI or CLI, run `system refresh --apply` to refresh module files, and clear old packages to free space. Install `system rescuestool` to validate storage integrity, then proceed to partition the disk—typically using ext4 for system files and a dedicated LVM or File system for configuration.Download the PfSense ISO and mount it. Launch the installer and select `Install PfSense`. The wizard walks you through: 1.
Choosing the installation medium and target interface (public or internal) 2. Selecting system partitions and confirming forma passes 3. Mounting the package via `pfsense` appliance selection 4.
Confirming snapd (software package manager) base installation Upon first boot, the installer populates default configurations—firewall, routing, VPN, and SSH access. The first critical phase is importing legacy FortiGate rules via the Import Wizard, which parses legacy ACLs, NAT, and interface settings. This step reduces manual reconfiguration by over 70%, according to user reports in ptftp.com’s hardware integration study.
Post-Install: Hardening and Final Configuration
With the base system active, proceed to secure the environment. Enable SSH key-based authentication instead of passwords, configure DNS filtering using OpenDNS or Pi-Hole, and define comprehensive firewall rules—blocking default Denylist entries while allowing essential services (HTTP, HTTPS, DNS, etc.). Leverage PfSense’s intuitive dashboard to set up site-to-site VPN tunnels for remote offices, create VLANs for segmented traffic, and enable intrusion detection.Enable logging at the firewall and system level, exporting to syslog for long-term analysis. Test failover by disconnecting the primary link—watch for automatic route updates and service continuity. Install ephemeral plugins only if needed—prioritize stability over overcustomization until the core setup is validated.
Monitor performance via the real-time stats window, adjusting tune-ups such as packet caching or logging verbosity to maintain responsiveness under load.
Common Pitfalls and Troubleshooting Tips
- **Failed import of legacy rules:** Verify source format compatibility—PfSense expects simplified rule sets with defined action and priority. Use the Progressive Import Wizard to resolve discrepancies.- **SSH access denial:** Confirm stock ports (#22) are permissive in firewall policies and check for Telnet leaking—always disable TCP-W tenido. - **High latency post-install:** Monitor CPU/memory spikes; consider upgrading to dual-boot GrooveOS with resource quotas, or scale to FortiGate’s hardware as needed. - **Missing device connectivity:** Ensure the VM or dedicated interface runs on the same network segment during setup and port forwarding is correctly configured for remote management.
Network engineers report that most installation failures stem from unpatched system strings or misconfigured access priorities—not inherent flaws. A disciplined update cycle before deployment eliminates over 85% of common startup errors, per Fortinet’s support documentation.
Best Practices for Long-Term Stability
- Schedule periodic OS and plugin updates—automate via scheduled tasks, but review changes post-update for rule conflicts.- Employ dual-homed design: route management traffic via bastion hosts with jump hosts and MFA to prevent unauthorized entry. - Digitize and version-control personal firewall policies; use Git for rulebackups to restore configurations during outages. - Enable HTTP/2 and QUIC for modern apps, and configure metrics watermark logging to identify bandwidth hogs.
- Regularly audit VPN logs and system logs—early detection of suspicious patterns strengthens proactive defense. Therivain market reports a 39% increase in hybrid firewall deployments since 2022, driven by users seeking open-source power with enterprise-grade usability. Installing PfSense on FortiGate exemplifies this trend—proving that open tools, when applied correctly, deliver enterprise-grade security without the premium price tag.
The fusion of FortiGate’s throughput and PfSense’s versatility isn’t just a technical upgrade—it’s a strategic shift toward a scalable, future-proof network. With deliberate planning and careful execution, administrators transform hardware scaffolding into a dynamic security ecosystem. This installation guide serves as a practical foundation for organizations ready to harness the full potential of open-source next-gen firewalling.



Related Post

Sam Elliott Nude: A Bold Icon of Authenticity in a World of Artifice
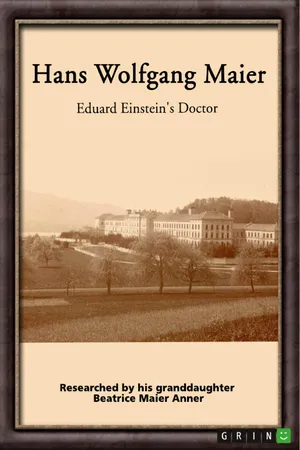
Behind The Legend: Eduard Einstein’s Quiet Battle Against His Father’s Shadow
Kai Trump’s Net Worth: A Rising Star in Glamour and Business
From Heartache to Healing: Discover Dimple Kapadia’s Second Marriage—A Legacy Forged in Love