Get To The Top Unblocked: Mastering the Art of Bypassing Digital Barriers
Get To The Top Unblocked: Mastering the Art of Bypassing Digital Barriers
In a world where digital access shapes education, commerce, and connection, navigating around internet restrictions has become both a necessity and a skill. From government-imposed firewalls to corporate content filters, digital barriers obstruct users across the globe—yet those determined to reach unblocked content are not helpless. The rising mastery of bypass techniques reveals a dynamic landscape where technology, strategy, and persistence converge.
Whether accessing global information, streaming cultural content, or maintaining open communication under restrictions, unlocking digital freedom is no longer a niche pursuit—it’s a critical competency in the modern era.
The Evolving Landscape of Digital Restrictions
Digital barriers manifest across geographies and purposes. State-level internet censorship in regions like China, Iran, and North Korea enforces strict content control, blocking foreign websites, social platforms, and independent media.These systems often use deep packet inspection, IP blacklisting, and DNS filtering to enforce compliance. Beyond government control, enterprises and schools deploy filters to restrict access to distracting or non-work-related websites—protecting productivity but sometimes at the cost of user autonomy. Meanwhile, users face restrictions in entertainment: streaming services remove content due to licensing, and geo-blocking limits access to region-specific media libraries.
What once seemed immutable now demands new approaches.
Key Tools and Techniques for Unblocking
Effective bypassing hinges on leveraging the right tools and understanding the underlying mechanisms of digital blockages. Among the most reliable solutions are: - **VPNs (Virtual Private Networks):** Encrypt internet traffic and route it through servers in unrestricted regions, masking user location and making geo-blocks transparent.- **Proxy Servers:** Serve as intermediaries\uff0a requests pass through the proxy, which then retrieves the blocked content undetected by conventional filters. - **Tor Network:** A decentralized network routing traffic through multiple encrypted relays, preserving anonymity but often with reduced speed. - **DNS Tunneling and Split DNS:** Bypass local DNS filtering by redirecting lookups to alternative, open DNS services—useful when entire domain blocks are enforced.
- **Browser-Based Tools:** Built-in hardened browsers or cache-extension hybrid tools can quietly bypass censorship layers without downloads. “Using a combination of these methods ensures layered protection and redundancy—critical when relying on a single bypass may fail,” says Maya Chen, a digital security expert at the Cyber Freedom Initiative. “Users must stay adaptable; as blocks evolve, so must their countermeasures.”
Strategic Approaches to Bypass Success
Bypassing digital barriers is not merely a technical exercise—it demands a strategic mindset.First, assess the **barrier type**: is it a regional geo-block, a DNS-level filter, or a full firewall? Each requires a tailored response. Next, evaluate **trade-offs**: speed versus anonymity, reliability versus security.
A speedy HTTP-based proxy might be fast but vulnerable; Tor offers strong anonymity but limited bandwidth. Users should also prioritize **authentication integrity**—fake credentials or improper VPN handshakes can trigger detection. Smart users layer tools: combining, for instance, a local proxy with a rotating VPN server adds resilience.
Monitoring for IP blacklists and regularly rotating access endpoints prevents sudden cordon offs. Organizations and individuals alike benefit from testing tools in controlled environments before full deployment. “Rushing bypass implementation increases false positives and detection risks,” advises Chen.
“Small-scale trials reveal quirks hidden in real-world usage.”
Real-World Use Cases and Effective Scenarios
Consider a student in a restricted region needing access to academic journals unavailable on local networks. By deploying a reputable VPN with a server in an open country, they regain seamless, encrypted access—turning educational obstacles into opportunities. Similarly, a freelancer in a nation blocking international collaboration platforms can use a proxy server to route traffic through unrestricted zones, allowing unimpeded use of cloud services.Journalists and activists often combine Tor access with encrypted messaging apps to communicate securely across blocked networks, preserving both information flow and personal safety. Even entertainment seekers manipulate digital barriers to unlock global streaming libraries. Despite geo-blocking, savvy users leverage international IP rotations—switching server least hours after market flips—to access region-locked shows.
These examples reflect a broader shift: digital restrictions concentrate power in gatekeepers, but determined users reclaim agency through layered access strategies.
The Ethics and Risks of Unblocking
Mastering the art of bypassing barriers carries ethical and practical considerations. While circumventing censorship supports freedom of information, misuse—such as circumventing institutional access policies or violating local laws—can lead to legal repercussions or heightened surveillance.Users face risks: compromised VPNs may log data; free proxy services often inject ads or malware. A responsible approach prioritizes **trusted, privacy-respecting tools**—prioritizing open-source solutions audited by security communities. “Unblocking isn’t inherently rebellious—it’s about informed resilience,” emphasizes Chen.
“Understanding local regulations and using tools transparently builds sustainable digital independence without unnecessary exposure.”
Best Practices for Secure and Sustainable Bypassing
To maximize efficacy and minimize risk, adopt these guidelines: - Choose end-to-end encrypted connections from vendors with clear no-logs policies. - Regularly update bypass tools to protect against known exploits. - Implement multi-factor authentication where available to secure access.- Avoid auto-connect features that expose location or identity inadvertently. - Combine techniques—proxy refresh with periodic VPN reauthentication—to counter rotational block attempts. - Stay informed on local digital policies to anticipate and avoid legal traps.
These steps forge a disciplined, proactive stance—transforming reactive circumvention into strategic empowerment.
In mastering the art of bypassing digital barriers, users transcend passive recipients of restricted access, becoming active navigators of an interconnected yet fragmented cyberspace. The tools exist, the knowledge is accessible—but true mastery lies in disciplined, ethical application.
As technological barriers grow more sophisticated, so must the skill, awareness, and initiative of those determined to reach the top, unblocked and empowered.



Related Post

Justin Swanstrom’s Net Worth: The Rising Star Behind the Success
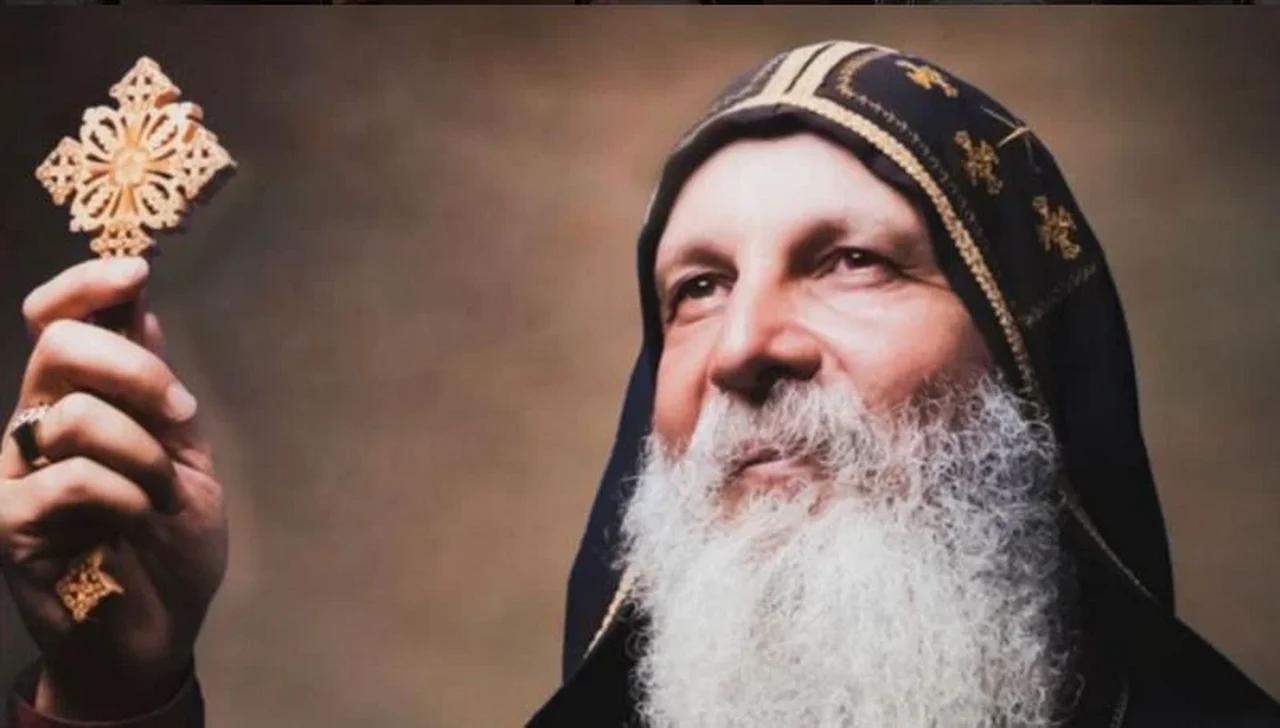
Bishop Mar Mari Emmanuel: How to Contact Him in Terms of Faith, Tradition, and Modern Accessibility
_-_Climate_Lab_Book_(Ed_Hawkins).png)
Andrea Henderson Husband: Bridging Science, Storytelling, and the Climate Movement

Meet NASCAR Legend Dale Earnhardt IV: The Driver Who Carries a Dynasty and Defies Legacy

