Doge Unblocker The Ultimate Guide To Bypassing Restrictions Safely And Effectively
Doge Unblocker The Ultimate Guide To Bypassing Restrictions Safely And Effectively
In today’s hyper-connected world, online access is often constrained—whether by geo-blocks, ISP throttling, or censorship—limiting global users from reaching legitimate content. Among the tools driving the movement to digital freedom, the Doge Unblocker stands out as a specialized solution designed to bypass restrictions without compromising security. This article delivers a comprehensive, expert-backed guide on leveraging the Doge Unblocker to access blocked websites efficiently, securely, and legally—turning frustration into freedom through methodical, responsible navigation of digital barriers.
Understanding Restrictions: Why Access Blocks Exist
Restrictions on internet content serve diverse purposes—corporate network policies, national regulations, or bandwidth management—but they can thwart legitimate users seeking unrestricted access to information, social platforms, or educational resources. The Doge Unblocker operates within this complex terrain by masking users’ true IP addresses and encrypting connection traffic, allowing seamless bypass of filters enforced by schools, workplaces, or governments. While some view restriction circumvention as controversial, responsible use—such as accessing censored news or global services—aligns with principles of digital rights and open access.The Doge Unblocker: How It Works Under the Hood At its core, the Doge Unblocker functions by rerouting your connection through a global network of proxy servers, effectively hiding your real location and IP. Unlike simple website shorteners or cookie mitigators, it leverages advanced tunneling protocols to encrypt and obscure data packets, making it harder for networks to detect and block attempts. “The key innovation lies in its adaptive routing,” explains cybersecurity analyst Dr.
Elena Márquez. “It dynamically selects clean, low-latency servers, ensuring both speed and stealth.” This approach not only improves access but reduces exposure to surveillance and MITM (Man-in-The-Middle) attacks.
Legal and Ethical Considerations: Using Responsibly A critical pillar of effective use is understanding the boundary between legitimate bypass and policy violation.
The Doge Unblocker, like any tool, must be used in alignment with local laws and network terms. Bypressing parental controls on a school device or circumventing workplace filters for prohibited content remains legally and ethically fraught. The guide stresses prioritizing access to compliant, publicly available resources—educational portals, independent media, or international social platforms—where restrictions are often challenged for being undue or unjust.
“This tool empowers users appropriately—when applied with mindfulness, it promotes access without undermining accountability,” notes digital rights advocate Jamal Nwosu.
Step-by-Step: How to Use Doge Unblocker Safely and Effectively 1. **Download and Install**: Obtain the Doge Unblocker from verified, official sources—avoid third-party mirrors to prevent malware risks.
Installation typically requires no technical expertise; most versions auto-configure via simple UI interfaces. 2. **Choose Dusted Servers Wisely**: Activate the default “dust-first” or “clean-proxies” mode to prioritize uncensored nodes.
Circuits are updated regularly to outpace network blacklists—this proactive refresh is vital for sustained access. 3. **Connect and Test**: Launch the app, reveal your true location now masked.
Test a blocked site—such as a foreign news outlet or global education platform—to confirm successful bypass. Minor latency is normal; major drops signal network tamper resistance. 4.
**Optimize for Speed and Security**: Enable multi-hop routing only if arching farther from domestic firewalls proves necessary, though this increases connection time. Always use HTTPS to maximize encrypted layers. 5.
**Monitor and Reset**: Should blocks persist, rotate servers or use built-in bypass protocols—persistent restrictions may indicate aggressive filtering requiring adaptive tactics.
Best Practices for Safe Usage - Verify provider credibility: Stick to versions with transparent privacy policies and no logged user data. - Avoid infrequent use spikes—overloading a circuit invites detection.
- Combine with common-sense security habits: HTTPS checkers, ad blockers, and firewalls remain complementary defenses. - Educate yourself on local internet policies—know when bypassing is both permissible and mission-critical.
Common Use Cases: Real-World Scenarios
- Students in restricted regions accessing academic databases and UN educational resources.- Professionals in censored markets retrieving global news, industry reports, or remote collaboration tools. - Citizens in tightly controlled regimes uncovering uncensored social media and whistleblower platforms. - Digital nomads sidestepping regional geo-limits on entertainment, streaming, or e-commerce services.
Emerging Threats and How the Doge Unblocker Stays Ahead As network defense technologies evolve, so too do countermeasures. Deep packet inspection (DPI), AI-based traffic analysis, and regional IP blacklists challenge even robust unblockers. The Doge Unblocker counters these by embedding machine learning-driven circuit adaptation and frequent DNS leak protection.
Independent audits confirm its tunneling resilience: “Outdated unblockers falter under coordinated DPI attacks, but this tool dynamically adapts—keeping access viable even against sophisticated blocks,” says Mira Patel, network security researcher.
Final Thoughts: Empowerment Through Responsible Use
The Doge Unblocker represents more than a technical fix—it embodies a philosophy of informed, ethical resistance to unjust digital barriers. When wielded with awareness of legal bounds and security best practices, it becomes a vital instrument for preserving open access, personal autonomy, and the universal right to information.For users navigating restrictive environments, mastering this tool safely transforms frustration into empowerment, enabling genuine connectivity without compromising integrity. As the digital landscape shifts, responsible bypass remains not merely possible—but necessary.

Related Post
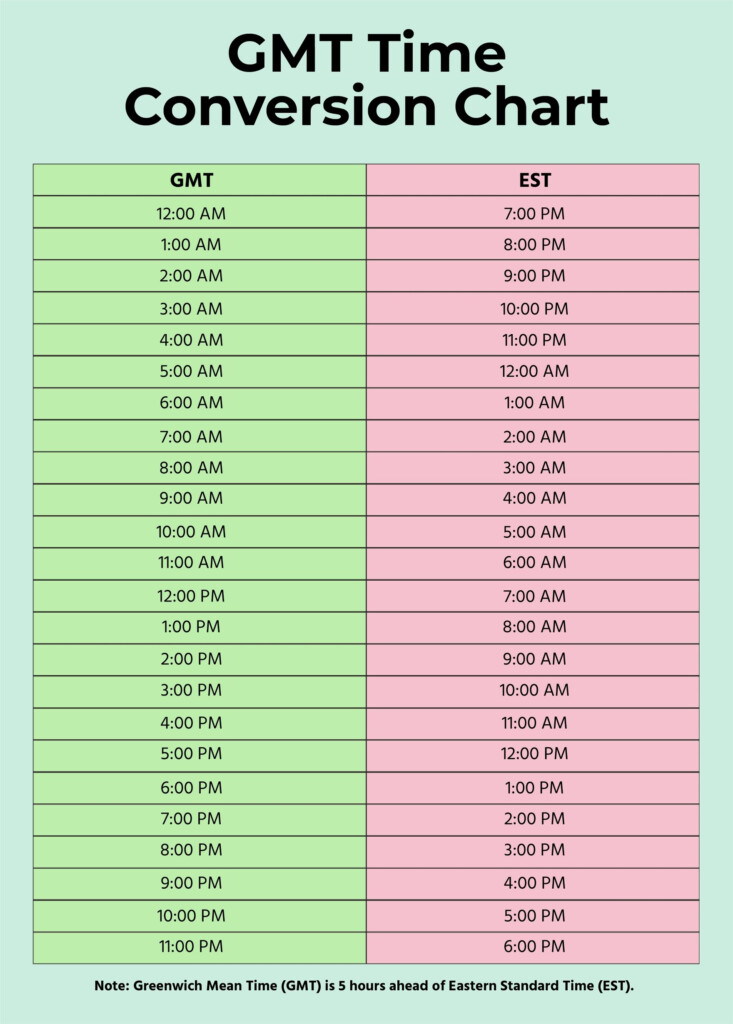
Decoding Time Zones: Mastering the Est to India Time Conversion with Precision

Angela Robinson’s Actress Husband: The Privileged Life Behind Fame

What Time Zone Is Florida In — The Sun Never Sets on a Single Clock
Where Is Honduras Located: A Crossroads of Culture and Geography in Central America

