Disabling Core Isolation and Memory Integrity: Windows’ Hidden Firewall Against Exploits
Disabling Core Isolation and Memory Integrity: Windows’ Hidden Firewall Against Exploits
In an era where advanced cyber threats exploit memory vulnerabilities with growing precision, Windows has evolved its defensive architecture with tools like Core Isolation and Memory Integrity—two powerful features designed to harden the operating system’s core defenses. These mechanisms act as a backstop against exploitation attempts that target memory corruption, privilege escalation, and remote code execution. By disabling or tightening control over these features, organizations and advanced users gain fine-grained authority to prevent or delay attacks before they breach the system’s most critical layers.
Core Isolation, a cornerstone of Windows Defender Advanced Threat Protection, functions by isolating high-privilege system processes into secure, lightweight virtual containers. This containment strategy ensures that even if an attacker compromises one process, the attack remains trapped and ineffective against the rest of the system. As explained by Microsoft security architect Ben Wil bases—“Core Isolation hardens the kernel surface by eliminating direct memory access between isolation domains, effectively chutting off common attack vectors like Return-Oriented Programming (ROP) and DLL hijacking.” This architectural separation significantly raises the bar for exploit success, especially in vulnerable Windows versions running legacy software.
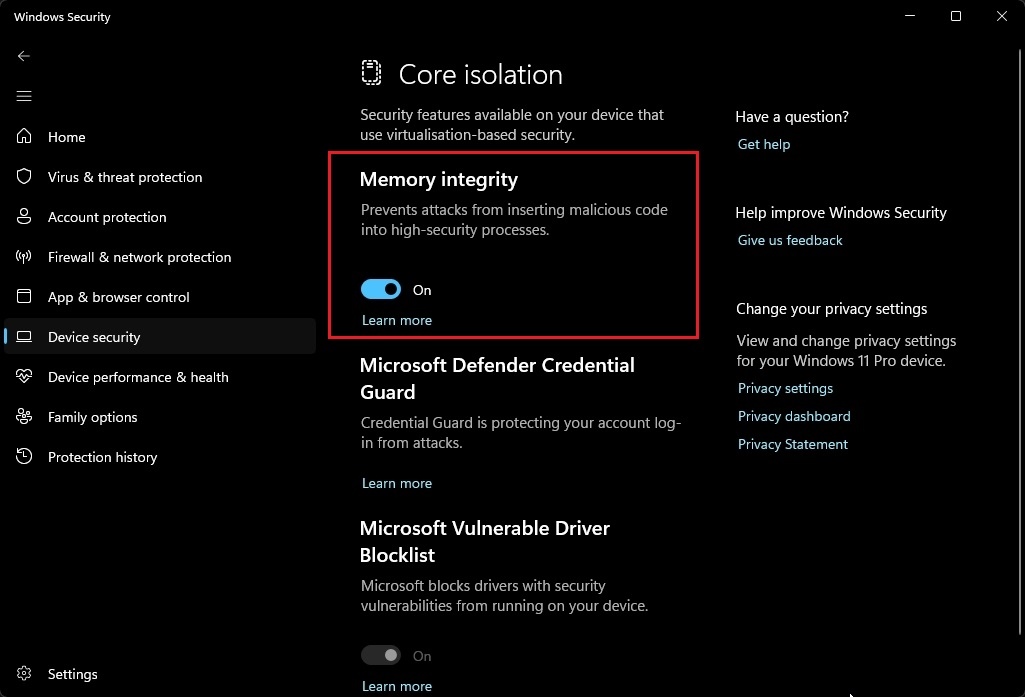
Equally vital is Memory Integrity, a component introduced to enforce strict memory access controls at the hardware level. Leveraging Windows’s Credential Guard and Virtualization-Based Security (VBS), Memory Integrity prevents unauthorized modifications to executable memory regions, detecting and blocking attempts to inject malicious code or alter critical kernel structures. According to Microsoft’s latest technical deep dive, “Memory Integrity validates memory integrity in real time using CPU-secured enumeration, flagging anomalies even when exploit code bypasses traditional code-signing checks.” This layer of protection operates transparently—without user intervention—ensuring systems remain resilient against zero-day exploits targeting memory"How-to", vulnerability exploitation“—even when defenses were previously reliant on patching alone.
Why now is the time to consider disabling these protections? While Core Isolation and Memory Integrity enhance security, their strict enforcement can interfere with specialized software environments, legacy applications, or performance-sensitive systems. Symantec’s cybersecurity analyst Lisa Tran notes, “In environments relying on unmanaged kernels, driver-based tools, or legacy virtual machines, aggressive isolation can introduce instability.” This forces tech leaders to balance robust protection with operational continuity.
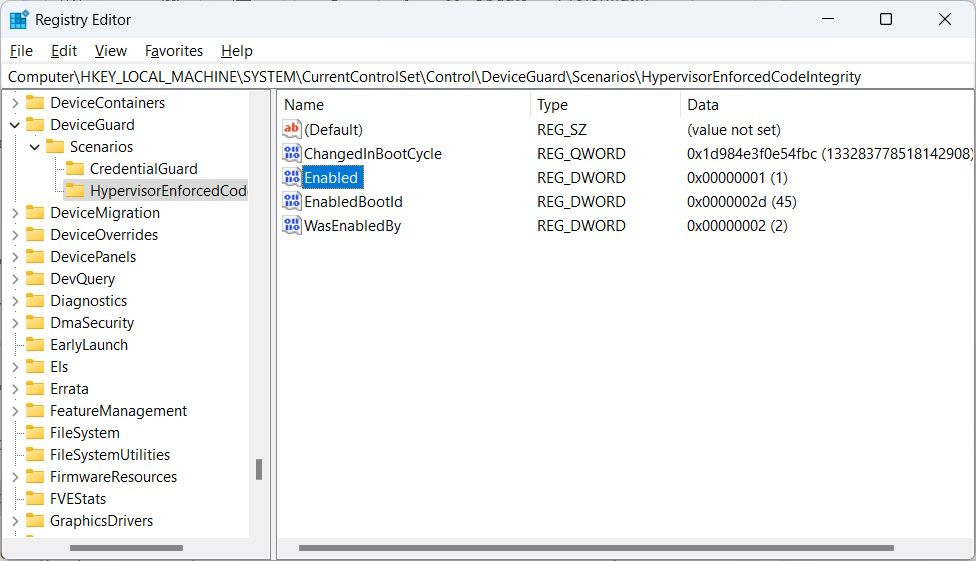
Users opting to disable or tweak these features must do so with caution, understanding that doing so effectively opens an attack window against memory-based exploits—including rote tables, buffer overflows, and adversarial kernel-level code injection. To implement control, Windows offers granular administrative tools: Group Policy Editor, PowerShell scripts, and Microsoft Endpoint Configuration Manager allow precise toggling. Disabling core isolation typically begins with disabling “Use Core Isolation for system processes” via Group Policy under *Computer Configuration → Administrative Templates → System*.
For Memory Integrity, administrators can disable specific memory validation rules using `Set-MpDpuPolicy` or analogous kernel policies, though caution is advised to preserve baseline secure states. Real-world impact matters. Testing isolated systems in controlled staging environments reveals that while non-essential services may run unfettered, defenders lose protection from avant-garde exploitation techniques such as Unfiltered NTRI (Non-Triggerable Return-Oriented Programming) and measured privilege escalations—primarily via software Christie’s technical report on advanced exploitation: “When Memory Integrity is disabled, attackers can manipulate executable memory regions undetected, effectively rewriting kernel logic or hijacking credentials at the memory level.” These attacks operate silently until lateral movement occurs, emphasizing the necessity of selective disablement—restricting, not abolishing, control.
Administration best practices recommend a defense-in-depth approach: enable isolation and integrity on critical systems while disabling them only where operational necessity outweighs risk. Monitoring logs via Windows Event Viewer and SIEM feeds helps identify exploit attempts post-disabling, enabling rapid response. Moreover, pairing these settings with Least Privilege enforcement and frequent patching forms a layered shield against persistent threats.
In essence, Disabling Core Isolation and Memory Integrity strips away essential firewalls built to intercept exploit payloads before exploitation. While tailored disablement supports operational agility, the trade-off is measurable: an exposed window vulnerable to some of the most sophisticated memory-based attacks Windows has deployed against. Staying informed, rigorously testing changes, and maintaining vigilant oversight ensures that any reduction in isolation doesn’t inadvertently invite catastrophe.
These tools are not stopgap measures—they are strategic controls demanding precision, justifying their use only with full awareness of risk and fortified by complementary defenses. The security posture of modern Windows systems hinges on this delicate balance: maintaining rigorous control over memory and execution while adapting to evolving threat landscapes. Core Isolation and Memory Integrity represent Windows’ most advanced cyber armor—but as with any armor, their protection must be wielded deliberately, not eliminated blindly.
In an arms race where memory remains the ultimate battleground, controlling this frontier is not optional. It is imperative.

Related Post
Mark Shera: The Unforgettable Actor Who Defied Hollywood’s Conventional Path

People Stunned as Wife’s Sting Becomes Focal Point of Shocking Social Phenomenon

Kathy Ireland’s Husband: A Bold Union Forged in Resilience, Support, and Style

Unveiling The Private Life Of Rachael Speed Beyond The Famous Link

