Cyber Tank: Revolutionizing Cybersecurity with Smart, Strong Defense Systems
Cyber Tank: Revolutionizing Cybersecurity with Smart, Strong Defense Systems
As digital threats grow more sophisticated, the urgency for next-generation cybersecurity solutions has never been greater. Enter Cyber Tank — a cutting-edge defense platform engineered to deliver intelligent, adaptive, and resilient protection across corporate, government, and critical infrastructure networks. By merging artificial intelligence, real-time threat intelligence, and automated response mechanisms, Cyber Tank is setting a new benchmark for how cybersecurity evolves in the face of relentless cyber warfare.
The digital battlefield is shifting. Advanced persistent threats (APTs), zero-day exploits, and ransomware campaigns now target organizations with unprecedented precision. In this high-stakes environment, legacy security systems struggle to keep pace—often reacting too slowly or lacking contextual awareness.
Cyber Tank addresses these limitations with a holistic architecture built for agility and foresight. At its core lies a smart defensive engine that learns from every attack vector, evolves defensive strategies autonomously, and enforces multi-layered protection with minimal human intervention.
Intelligent Threat Detection Powered by Adaptive Intelligence
Cyber Tank’s defining feature is its adaptive threat detection system, which leverages machine learning models trained on vast datasets of known and emerging cyber threats. Unlike static signature-based engines, this dynamic engine interprets behavioral patterns in real time to identify anomalies and suspicious activities before they escalate into breaches.- The system ingests data from network traffic, endpoint logs, user behavior analytics, and global threat feeds to construct a comprehensive threat landscape. - Advanced algorithms detect subtle shifts—such as unusual data transfers, cryptographic anomalies, or unauthorized privilege escalations—flagging threats with high accuracy. - Behavioral profiling differentiates between legitimate user actions and malicious intent, minimizing false positives while maximizing detection coverage.
“This platform doesn’t just react—it anticipates,” says Dr. Elena Rostova, Lead Cybersecurity Architect at InnovationX, a global IT security firm rigorous in testing next-gen defense systems. “Cyber Tank’s cognitive approach transforms passive monitoring into proactive, context-aware defense.”
By continuously updating detection models based on real-world attack data, Cyber Tank maintains exponential improvement in threat recognition—offering a critical edge against stealthy, evolving cyber adversaries.
Orchestrated Defense with Automated Response Capabilities
Once a threat is identified, Cyber Tank’s integrated response framework activates with surgical precision.Automated protocols isolate compromised nodes, quarantine affected systems, and deploy countermeasures without disrupting normal operations. Orchestrated across distributed environments—from cloud platforms to on-premises networks—this response system reduces mean time to containment from hours to seconds. - Security orchestration tools coordinate responses across firewalls, endpoint protections, and identity management systems.
- Predefined “playbooks” align incident actions with organizational policies, ensuring compliance and consistency. - Real-time dashboards provide security teams with actionable insights, enabling efficient oversight and strategic decision-making. The platform’s automation doesn’t replace human expertise—it amplifies it.
Analysts focus on high-priority threats while routine containment and remediation tasks are seamlessly engineered by Cyber Tank’s intelligent automation, freeing resources for strategic threat hunting and long-term resilience planning.
Scalability and Flexibility Across Diverse Environments
One of Cyber Tank’s most compelling advantages is its scalability. Designed to protect environments ranging from small enterprises to multinational organizations, the system runs efficiently in hybrid, multi-cloud, and edge computing infrastructures.Modular architecture allows deployment across disparate security stacks, integrating with existing tools—SIEMs, firewalls, and IAM solutions—while maintaining a unified threat management interface. - Cloud-native deployment supports rapid scaling to meet fluctuating workloads and geographic expansion. - Containerized components ensure consistent behavior across on-premises and cloud environments.
- API-driven integration enables automated data exchange with third-party security tools, fostering a cohesive, forward-thinking ecosystem. “Cyber Tank bridges gaps between legacy infrastructure and modern cloud demands,” notes cybersecurity consultancy Nexis Shield. “It transforms fragmented security tooling into a synchronized defense net—no matter how complex the digital footprint.”
Real-World Impact: Securing Critical Infrastructure and Enterprise Networks
Rollouts of Cyber Tank in recent high-profile deployments underscore its transformative impact.In a groundbreaking case, a leading European utility provider implemented the system to protect its grid control networks from advanced cyber intrusions. The platform’s real-time anomaly detection thwarted an attempted disruption of power distribution systems, preventing cascading failures and potential public safety risks. - Critical infrastructure operators report reduced alert fatigue, fewer blind spots, and faster confidence in system integrity.
- Enterprises in finance, healthcare, and manufacturing have demonstrated measurable improvements in compliance, breach containment speed, and executive visibility into cyber risk posture. These outcomes signal a new paradigm: cybersecurity no longer a peripheral safeguard, but a strategic enabler of digital trust and operational continuity.
Human-Machine Collaboration: The Bridge to Resilient Cybersecurity
Despite its technological sophistication, Cyber Tank emphasizes human-machine synergy.The user interface is intentionally designed for security analysts—intuitive, transparent, and supportive. Dashboards present complex data in digestible visual formats, with customizable alerts and prioritized threat rankings. Security teams leverage the platform not only to manage threats but to cultivate deeper strategic insight.
As Dr. Rostova notes, “The best security isn’t about replacing humans—it’s about empowering them with faster, smarter insights.” Cyber Tank’s architecture reflects this philosophy: intelligent automation handles the reactive heavy lifting, while skilled professionals guide long-term security strategy and fine-tune defensive nuances.
Preparing for the Future: AI-Driven Defense in an Evolving Threat Landscape
Looking forward, Cyber Tank positions itself at the forefront of AI-driven cybersecurity innovation. The platform is designed to integrate emerging technologies—including generative AI for attack simulation, quantum-resistant cryptography, and federated learning for decentralized threat modeling.These enhancements promise not just defensive resilience, but adaptive evolution across generational shifts in cyber threats.
As the global threat landscape grows more complex, Cyber Tank demonstrates how smart, strong defense systems are not merely optional—they are essential. By embedding intelligence at every layer, enabling seamless automation, and fostering human-centric collaboration, this system redefines what robust cybersecurity truly means in the digital age.
In a world where cyber attacks can disrupt economies and endanger lives, Cyber Tank delivers the precision, agility, and scalability required to safeguard the future.
It stands as a testament to innovation driven by real needs, proving that the next generation of defense is not just smart—it’s stronger, faster, and infinitely more proactive. The revolution in cybersecurity isn’t coming—it’s already underway, powered by platforms like Cyber Tank.


Related Post
Dr. Dre’s Children: Beyond the Beats — The Next Generation Shaping Culture, Sound, and Success

Peugeot 407 SW 2007: Unveiling the Versatile Family-Sedan Live Longer
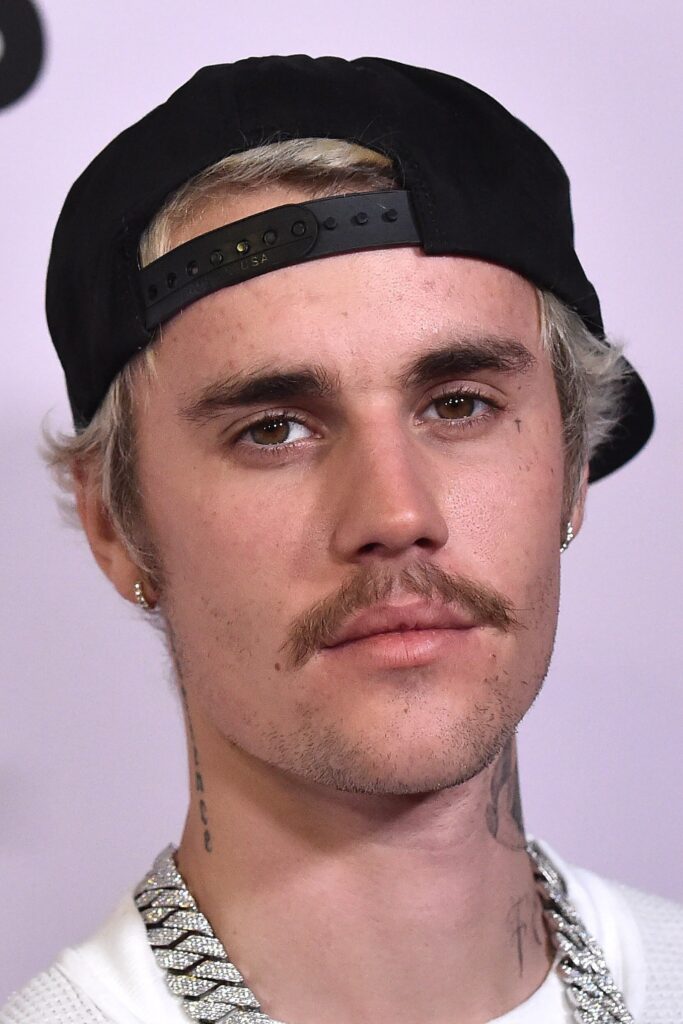
Justin Bieber at 40: Unpacking the Age That Forged a Global Music Icon

Reginald Veljohnsons Life Family Matters: The Quiet Legacy Behind a Television Icon