Coinbase Scams: How to Spot and Stop the Most Common Threats Before They Strike
Coinbase Scams: How to Spot and Stop the Most Common Threats Before They Strike
In an era where digital assets dominate financial conversations, Coinbase remains one of the most trusted platforms for buying, selling, and storing cryptocurrencies—yet it is not immune to scams. As adoption grows, so does the sophistication of fraudsters exploiting user trust, technical vulnerabilities, and human psychology. Whether through phishing emails, fake customer support calls, or deceptive trading interfaces, scammers are constantly refining their methods to bypass security.
Understanding current tactics and adopting proactive defenses is no longer optional—it’s essential for anyone holding crypto. This article exposes the most pervasive Coinbase scams and provides actionable strategies to safeguard your digital wealth with precision.
One clear pattern emerging in 2024 is the shift from generic phishing to highly personalized social engineering.
Scammers now gather personal data from public sources—social media profiles, published portfolios, or even leaked details—to craft convincing messages that appear to come from real support agents or trusted community members.
Recognize the Red Flags of Common Coinbase Scams
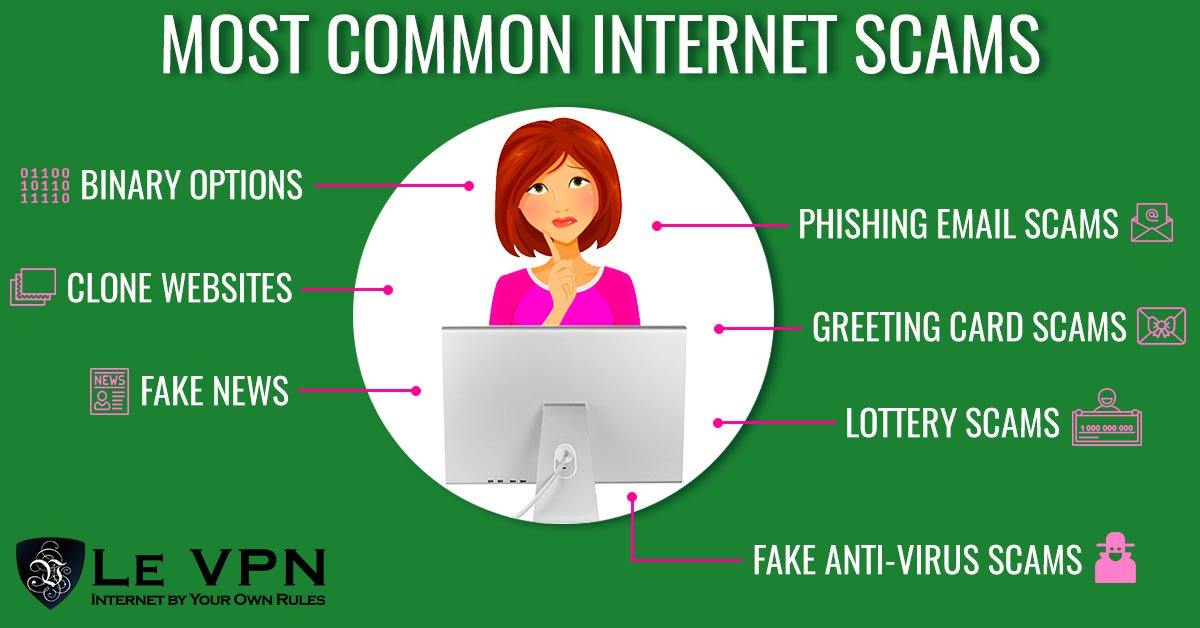
Scammers exploit emotional triggers and perceived urgency to override rational judgment. Among the most prevalent threats are:- Impersonation Phishing. Attackers deploy emails, SMS, or fake Coinbase login pages designed to mimic official interfaces. These messages often warn of account suspensions, login breaches, or pending verification steps, pressuring users to click malicious links.
The emails frequently include urgent language like “Your account is locked—click now to reactivate.”
- Fake Withdrawal Support Scams. Scammers pose as Coinbase technical support, claiming your account has unusual activity requiring immediate funds transfers to “secure wallets.” Victims send crypto to fraudulent wallets, losing funds permanently. One documented case involved 37 victims losing over $400,000 combined through this method.
- Romance and Investment Scams. Romantic scammers build trust online, then fabricate Coinbase success stories—fake investment gains or story-driven trading wins—then request crypto donations under the guise of “future returns.” Similarly, pump-and-dump schemes masquerade as exclusive investment opportunities.
- App and Wallet Impersonation. Malicious developers release fake Coinbase-style apps or wallet interfaces with nearly identical UI, tricking users into entering login details or private keys, which are harvested instantly.
How to Verify Legitimate Communication and Support Channels
A simple yet powerful defense against impersonation lies in proactive verification. Coinbase maintains strict policies against unsolicited contact, and legitimate support never demands immediate login credentials, 2FA codes, or direct sharing of private keys.Always verify communication by:
- Checking official domains: Only use the Coinbase website (coinbase.com) or verified app stores; official notifications appear in your account dashboard, not via email or text unless explicitly initiated by you.
- Verifying support agents: New customer service reps will never pressure you to disclose your account’s security questions or suddenly reset your password with unsolicited requests.
- Avoiding demo accounts or fake “tech support” pages: If a message asks you to click a link claiming to connect your mobile device to “fix” an account issue, treat this as a high-risk red flag—if in doubt, close the tab and navigate directly to coinbase.com.
Securities and Exchange Commission warned that consistent red flags include requests for 2FA codes via message, urgent account freezes, and login errors demanding immediate action. These are not standard Coinbase practices—for real support, users should initiate contact through verified channels only.
Fortify Your Account Security with Multi-Layered Defenses
Even with vigilant awareness, robust technical defenses are critical.Start with enabling 2-factor authentication (2FA) using authenticator apps instead of SMS, which is vulnerable to interception. Enable Coinbase’s extended security features, including login alerts, unusual activity notifications, and the ability to disable account access from new devices.
Adopt these layered protections:
- Use strong, unique passwords: Avoid reused or predictable passwords.
A password manager ensures account-specific entries remain secure and accessible only to you.
- Backup recovery keys carefully: Store Coinbase’s encrypted recovery keys offline—never in cloud services or unprotected devices. Use hardware wallets or encrypted digital vaults for maximum safety.
- Regularly audit connected wallets and devices: Review recent login activity and active devices in the “Security” dashboard. Remove any unfamiliar sessions immediately.
- Enable email/SMS alerts: Activate notifications for logins, password changes, and crypto movements so suspicious activity is flagged within minutes.
Combining skepticism with technical safeguards forms the foundation of resilience.
Spotting Social Engineering: The Human Element in Crypto Security
Scammers thrive on exploiting cognitive biases—urgency, fear of loss, desire for quick gains, and social trust. Recognizing psychological manipulation is as important as technical vigilance.For example, a phishing email warning of “suspended funds” triggers anxiety, prompting hasty clicks. Someone rushing to remove a fake “security alert” rarely pauses to verify legitimacy.
Develop a reflexive mindset: when confronted with pressure, interrupt.
Pause. Ask: Would Coinbase really require this action so urgently? Is this request in line with official communication channels?
Sometimes, waiting 15–30 minutes before responding exposes a scam.
Community forums and verified user reports consistently highlight helplessness as a vulnerability. But awareness transforms fear into action—users who pause and verify are far less likely to fall victim.What to Do If You Suspect Fraud
Despite precautions, breaches can occur.Immediate, decisive action minimizes damage. If share confidential data or transfer crypto to a fraudulent wallet:
- Freeze transactions instantly: While Coinbase does not guarantee full recovery of stolen funds, reporting the incident immediately halts further movement.
- Change passwords and enable enhanced security: Revoke all compromised credentials and tighten access controls.
- Submit a report: Contact Coinbase’s fraud reporting team via in-app support with screenshots of suspicious activity. Notify the FBI’s Internet Crime Complaint Center (IC3) and your local cybercrime unit.
- Monitor financial accounts: Check bank statements and crypto exchanges for unauthorized activity.
Early intervention dramatically improves outcomes.
The Ongoing Battle: Staying Ahead of Evolving Scams
Coinbase scams are not static threats but a dynamic challenge shaped by technological innovation, user behavior, and criminal adaptability. The story doesn’t end with awareness.Users must remain active guardians—updating knowledge, reinforcing habits, and supporting a culture of skepticism combined with action. Organizations like the Better Business Bureau and global financial watchdogs continue raising public awareness, but individual responsibility is equally crucial. The digital future demands trust—but trust must be earned through vigilance.
By mastering the red flags, fortifying security, and staying intellectually alert, users transform confusion into confidence. In an age where crypto represents real economic power, protecting oneself is not just smart—it’s essential. This comprehensive defense framework, grounded in verified threats and expert consensus, empowers every Coinbase user to navigate the space with clarity and control.
Only through sustained attention and informed action can the risks of scams be effectively contained.

Related Post

How Many Kids Does Nelly Have? The Family Size Behind the Spotlight

Weight Holly Marie Combs Now: The Evolving Journey of a Star’s Curvaceous Legacy

Footybit: Revolutionizing the Footy Experience with Smarter Data and Deeper Insights

Maria Del Refugio Abarca Villaseñor’s Children: A Family Legacy Shaped by Resilience, Culture, and Purpose

