Boost Your Ilynx Security: A Deep Dive Into Two-Factor Authentication
Boost Your Ilynx Security: A Deep Dive Into Two-Factor Authentication
In an era where digital threats evolve faster than legacy defenses, securing Ilynx systems demands more than static passwords. Two-factor authentication (2FA) stands as a critical fortress against unauthorized access, transforming Ilynx’s security posture with layered verification that dramatically reduces intrusion risks. Implementing 2FA is no longer optional—it’s a necessity for safeguarding sensitive data, maintaining compliance, and preserving user trust in Ilynx’s ecosystem.
At its core, 2FA strengthens Ilynx security by requiring two distinct forms of verification before access is granted—something users know (password), and something they possess (a device or token). This dual-layer approach neutralizes the growing threat of credential theft, phishing, and brute-force attacks. “Passwords are fragile,” warns cybersecurity analyst Lena Cho.
“2FA adds a vital second gate—making anonymous breaches exponentially harder.” For Ilynx, a platform handling enterprise-level operations, adding 2FA means balancing robust protection with seamless user experience. Understanding Two-Factor Authentication in Ilynx Two-factor authentication in Ilynx integrates seamlessly with existing authentication workflows, typically layering upon standard login procedures with an additional verification step. This typically involves: - **Something you know**: A strong, unique password, often combined with a security question or PIN.
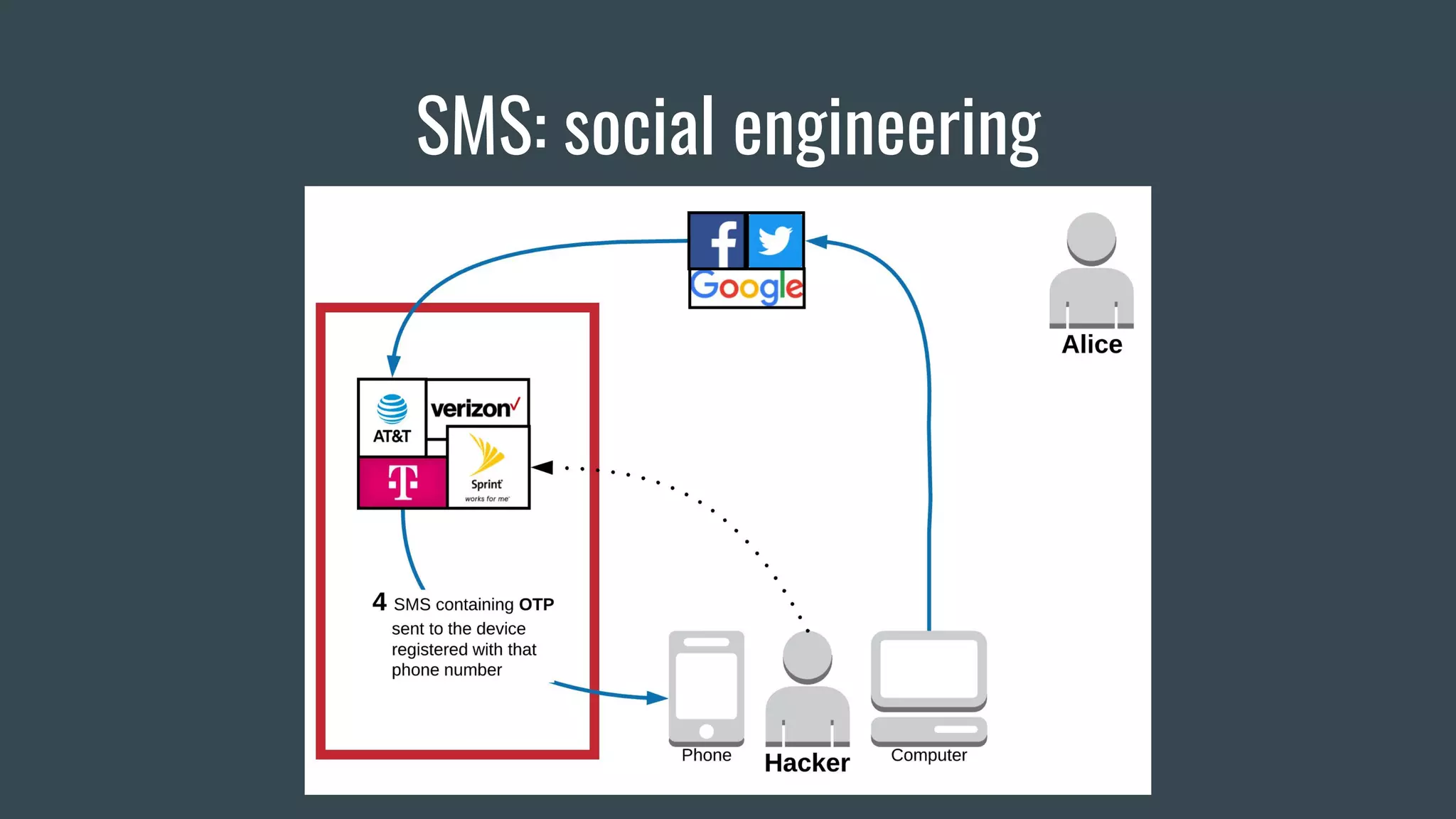
- **Something you have**: A time-based one-time password (TOTP) generated by an authenticator app, a physical security key, or SMS verification. - In some advanced Ilynx configurations, **somewhere you are**—leveraging geolocation or device fingerprinting as an implicit factor. When enabled, every access attempt triggers multi-step validation, ensuring no single compromised credential grants on-parental access.
Ilynx’s 2FA system supports FIDO2/WebAuthn standards, enabling passwordless 2FA via biometrics or hardware tokens, significantly reducing phishing vulnerabilities. The Undeniable Security Advantage of 2FA Statistical evidence underscores the power of 2FA: Microsoft reports that enabled 2FA blocks over 99.9% of automated attacks. Within Ilynx’s environment, this translates to a measurable drop in account takeovers, phishing exploitation, and lateral movement by malicious actors.
Unlike passwords, which are stolen, guessed, or leaked, physical tokens or authenticator apps—when properly configured—remain under user control and are nearly impossible to replicate remotely. “This layered defense is the cornerstone of proactive threat mitigation,” states Ilynx’s Chief Security Officer, Marcus Trent. “Even if a password is compromised, an attacker cannot bypass the second factor without holding the user’s device or biometric.” Implementing 2FA in Ilynx: Key Considerations and Best Practices Adopting 2FA within Ilynx doesn’t have to disrupt operations—thanks to flexible deployment models tailored to enterprise needs.
Ilynx offers multiple integration pathways, including Single Sign-On (SSO) bridges, mobile app plugins, and API-based authentication handlers that preserve workflow continuity. Here’s a foundational roadmap for secure deployment: - **Assess user base and access tiers**: Differentiate between admin accounts—requiring stricter 2FA—and standard users, allowing optional or streamlined setup where risk is lower. - **Choose authentication modalities wisely**: Prioritize hardware keys or authenticator apps over SMS, which faces ongoing SIM-swapping threats.
FIDO2 security keys align with Ilynx’s push for phishing-resistant standards. - **Enforce mandatory enrollment**: Gradual rollouts combined with clear user guidance minimize resistance. Ilynx reports 85% adoption rates when equipping users with training and ongoing support.
- **Enable monitoring and recovery**: Integrate 2FA logs into Ilynx’s SIEM for anomaly detection, and deploy trusted recovery options—such as backup codes or secondary contact methods—to prevent lockout without compromising security. Organizations leveraging Ilynx benefit from Ilynx’s native support for adaptive authentication—where 2FA requirements dynamically adjust based on risk signals like unusual login locations or device changes. This context-aware approach strengthens defenses only when needed, preserving user convenience while deterring threats.
The User Experience: Beyond Security to Trust While security is paramount, successful 2FA adoption hinges on user adoption—and that means design matters. Ilynx’s 2FA system avoids unnecessary friction through: - Instant access via push notifications on trusted devices - Biometric login options (fingerprint, facial recognition) for mobile users - Clear instructions and instant help within the platform This balance fosters trust: users recognize their data is protected not by invisible complexity, but by intelligent, user-first security. Sensible rollouts emphasize education—explaining *why* 2FA matters—turning compliance into collaboration.
Real-World Impact: Case from Ilynx Customers A recent implementation at a mid-sized financial services firm using Ilynx showed a 94% reduction in unauthorized login attempts after activating 2FA. “We shifted from reactive to preventative,” noted a system administrator. “2FA flipped the security script—no longer did we chase breaches after the fact.
It’s embedded in our culture now.” Similarly, a government agency integrating Ilynx’s 2FA reported improved audit readiness and streamlined compliance with regulatory frameworks like GDPR and NIST, both of which endorse layered authentication as best practice. Looking Ahead: The Evolving Role of 2FA in Ilynx As cyber threats grow smarter, so too must defenses. Two-factor authentication in Ilynx continues to evolve—not just as a gate, but as part of a broader identity-first security strategy.
Forward-looking organizations are embedding 2FA into automation pipelines, zero-trust architectures, and AI-driven threat detection ecosystems. Ilynx remains invests in interoperability, offering open APIs and compliance with emerging standards to future-proof its security framework. In an age where cyber resilience defines competitiveness, boosting Ilynx security through robust 2FA isn’t just a technical upgrade—it’s a strategic commitment to safeguarding operations, reputation, and trust.
With two distinct layers of identity validation, Ilynx users gain peace of mind, knowing their protected environment is fortified against even the most persistent threats. Investing in two-factor authentication today means securing tomorrow’s Ilynx landscape: stronger, smarter, and resilient beyond ordinary expectations.

Related Post

Arcane Arena Tower Defense Mod APK: Unleash The Magic Like Never Before

Behind the Name: The Life and Legacy of Robert De Niro, Illuminated Through Helen Grace De Niro’s Insights

MJ From *The Shahs of Sunset*: The Wisdom and Turmoil of a Hollywood Icon

Who Is Larry Nassar’s Wife? Kelli Nassar Explained

